Thanks for the tip!
-
-
But that's not true. I can set a PNG as executable.
-
@ben_lubar said in Thanks for the tip!:
But that's not true. I can set a PNG as executable.
And you can execute it. Violently, and with prejudice.
-
@ben_lubar said in Thanks for the tip!:
But that's not true. I can set a PNG as executable.
#BuggyLunixHardware
-
@error said in Thanks for the tip!:
And you can execute it
If Linux is anything like Windows, all "running" a png does is invoke a handler.
-
@FrostCat said in Thanks for the tip!:
@error said in Thanks for the tip!:
And you can execute it
If Linux is anything like Windows, all "running" a png does is invoke a handler.
IIRC, the original iPhone jailbreak was a malformed png exploiting a buffer overflow in Mobile Safari.
Filed under: I wanted so badly to go to an Apple Store and load that URL on all of them.
-
@error said in Thanks for the tip!:
Filed under: I wanted so badly to go to an Apple Store and load that URL on all of them.
people did, more then once.
-
@FrostCat said in Thanks for the tip!:
If Linux is anything like Windows, all "running" a png does is invoke a handler.
Does "runing" mean "clicking on some icon in a file manager" in Windows? That might be the same. Unless you really did set the file to be executable, in which case it might try to actually execute the file instead. I guess that depends on the file manager.
-
Does "runing" mean
 , not
, not  .
."clicking on some icon in a file manager" in Windows
Effectively, yes. If the file's type is registered, Windows will go "ok, you must want to open your filie with $registered_handler (e.g., paint or whatever.) I assume that's what Linux et al do as well.
Technically that's not the same as "load the file contents into memory and then tell the CPU to treat them as machine code," even if the aforementioned exploit had the same ultimate effect.
Unless you really did set the file to be executable
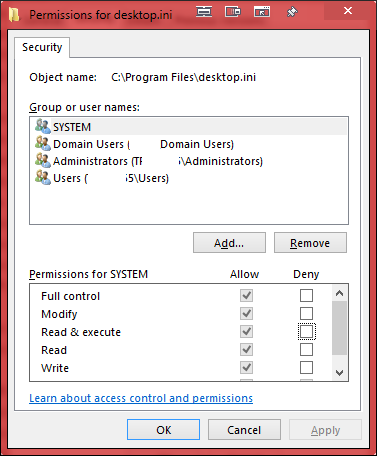
In Windows, there's a permission "read and execute" and images probably already have it, as well as "read", so probably not.
-
@FrostCat said in Thanks for the tip!:
"load the file contents into memory and then tell the CPU to treat them as machine code,"
A lot of executable code doesn't work this way either. With Java or .NET you're dealing with a JVM or JIT compile step between the executable and the bare metal.
-
@error said in Thanks for the tip!:
A lot of executable code doesn't work this way either.
Right. But a JAR (for example) is going to be handled like a PNG: Windows says "oh, I need to fire up a handler (the JVM) and pass the file on to it.
.Net executables, as far as I know, aren't treated that way--they're actually executed, but then the loader knows to pass the file off to a .Net VM.
-
@FrostCat where problem?
An executable file is a file that can be directly executed. Marking a file as executable, even providing a default handler for certain file types, does not make it directly executable.
I'm not sure what Windows does is even directly execute as ISTR even .exe has a "default handler" of sorts.
-
@Arantor said in Thanks for the tip!:
even .exe has a "default handler" of sorts.
Yeah, that's a fun worm to get rid of when it replaces that with itself.
-
@Arantor said in Thanks for the tip!:
where problem?
Re-read that first sentence. It's a tautology. An executable file is a file that can be executed? That sentence imparts no new information.
I'm not sure what Windows does is even directly execute as ISTR even .exe has a "default handler" of sorts.
Well the "handler" is the OS itself, or rather the loader.
-
@FrostCat said in Thanks for the tip!:
.Net executables, as far as I know, aren't treated that way--they're actually executed, but then the loader knows to pass the file off to a .Net VM.
IIRC, the first versions of .NET worked that way during the transitional phase, but newer versions of Windows recognize .NET executables as special and handle them specially.
-
@FrostCat The first rule of the tautology club is the first rule of the tautology club.
-
I assume that's what Linux et al do as well.
Not really. If you try to execute an arbitrary file, it will get passed to the loader, which will barf "exec format error" if it's not an ELF binary or whatever format your architecture uses. At some point in the process (I don't remember off-hand whether it's the loader or whether it's checked before it gets handed to the loader, and I CBA to check), if it's a text file, it gets passed to the default shell, which will try to interpret it and spew syntax errors.
... Actually, it looks like the error message is coming from the shell. I'm not sure without further investigation whether it's checking the file type or just reporting the error from the exec() syscall.
-
@FrostCat by any user definition, a PNG file executes an action: it loads Photoshop. It isn't executable but something executes anyway.
An executable file just executes itself.
You're trying to apply
 to a definition not meant for technical people, where it is perfectly cromulent.
to a definition not meant for technical people, where it is perfectly cromulent.
-
@Arantor said in Thanks for the tip!:
@FrostCat where problem?
An executable file is a file that can be directly executed. Marking a file as executable, even providing a default handler for certain file types, does not make it directly executable.
I'm not sure what Windows does is even directly execute as ISTR even .exe has a "default handler" of sorts.
Windows needs a default handler for .exe files because it doesn't have any concept of an "executable flag".
-
@anotherusername said in Thanks for the tip!:
"executable flag".
Sure it does! It's just that it's basically the same as "read"!

-
@anotherusername said in Thanks for the tip!:
@Arantor said in Thanks for the tip!:
@FrostCat where problem?
An executable file is a file that can be directly executed. Marking a file as executable, even providing a default handler for certain file types, does not make it directly executable.
I'm not sure what Windows does is even directly execute as ISTR even .exe has a "default handler" of sorts.
Windows needs a default handler for .exe files because it doesn't have any concept of an "executable flag".
I once had a piece of malware that installed itself as the handler for
.exefiles. I unwisely deleted it.I couldn't even launch
regeditto remove the handler, because that's an exe. I think I renamed it to.comor something.
-
@error said in Thanks for the tip!:
I once had a piece of malware that installed itself as the handler for .exe files
I
 d you there. ;)
d you there. ;)
But yes, that was definitely fun.
Luckily all I had to do was netboot the thing and edit the registry offline, but you probably had more fun live-patching the system.
-
@Tsaukpaetra execute permission != executable flag.
-
@anotherusername said in Thanks for the tip!:
@Tsaukpaetra execute permission != executable flag.
I see you missed my
 there.
there.
Lets make it a white face, just in case you're on dark theme:
-
@Tsaukpaetra said in Thanks for the tip!:
I
 d you there.
d you there.D'oh!
Filed under: The quote button removed the emoji. I manually reinserted it., CC @ben_lubar
-
@error said in Thanks for the tip!:
The quote button
removedisn't even aware of the emoji.FTFY. The select-quote thing isn't aware of formatting (such as emoji, italics, etc), just whatever text is there.
-
@Arantor said in Thanks for the tip!:
You're trying to apply to a definition not meant for technical people
No, I'm asserting that isn't a meaningful definition. "A foonting turlingdrome is a turlingdrome that foonts".
-
Also, 27 posts in (28 now) and nobody's
 'd the title.
'd the title.
-
@FrostCat Nobody ever thanked someone for the
 tip. The whole
tip. The whole  maybe :)
maybe :)
-
@FrostCat said in Thanks for the tip!:
An executable file is a file that can be executed?
It defines the term "executable file". So yeah, the definition of "executable file" is "a file which can be executed". That's how definitions work, somethimes they're redundant, but that doesn't make them wrong.
Either way:
"Ran" is a synonym for "executed", so this definition is just as redundant - but it's right. For another example, off the top of my head:
Totally redundant, but that's how definitions work.
-
@FrostCat said in Thanks for the tip!:
If Linux is anything like Windows, all "running" a png does is invoke a handler.
On Linux there's clicking on a file in a file manager which does whatever the file manager wants, hopefully something as smart as looking for a handler. Then there's also the exec() syscall which requires kernel support for any file you wish to execute. Most executable files are ELF but there are other formats. There is (was?) a binfmt_java module that makes .jar files directly executable, for example.
-
@HardwareGeek said in Thanks for the tip!:
... Actually, it looks like the error message is coming from the shell. I'm not sure without further investigation whether it's checking the file type or just reporting the error from the exec() syscall.
The
execve()system call (there's a bunch of wrappers round it, but that's the real one) can directly handle scripts, provided they're marked as executable at all in the file metadata and have the appropriate “magic number” set. Which is what the leading#!is all about; the rest of the line says what the kernel is to do to run the file (and typically has to start with a/because the kernel doesn't doPATHsearching).@another_sam said in Thanks for the tip!:
There is (was?) a binfmt_java module that makes .jar files directly executable, for example.

-
@dkf said in Thanks for the tip!:
The execve() system call ... can directly handle scripts
Thanks for the clarification. I didn't remember where in the flow the decision of directly executable vs. invoke an interpreter/handler was made and CBA to look it up, especially on mobile.



 . Apparently,
. Apparently, execve()doesn't, itself, generate the error message, just returns the failure code to its caller, because the error message was definitely prefixed withzsh: ....
-
@Arantor said in Thanks for the tip!:
a PNG file executes an action: it loads Photoshop
Nope. Not on my computer.
It loads rather, it results in the OS loading GIMP.
-
@HardwareGeek said in Thanks for the tip!:
Apparently,
execve()doesn't, itself, generate the error message, just returns the failure code to its caller, because the error message was definitely prefixed withzsh: ....The
perror()library function can do that sort of thing, but nobody's obligated to use it. It's purely a convenience thing.
-
@HardwareGeek you double click it, an action is executed.
 denied :P
denied :P