A small security update
-
I went to my bank's website to pay my bills, when I was met with this message:
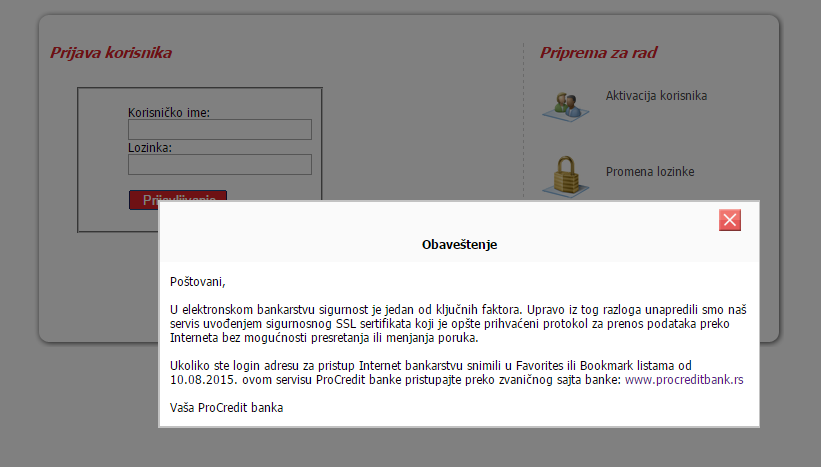
Dear customer,
In electronic banking, security is a key factor. For this reason, we have improved our service by introducing security SSL certificate that is widely accepted protocol for data transmission over the Internet without the possibility of interception or alteration of communication.
Oh, cool. Always nice to see banks are improving their security....
Wait a sec. They just now added SSL!?
WHAT THE FUCK WERE THEY USING 'TILL NOW!?
-
My guess: Obscurity + rot13 + XOR. Minus up to three.
-
-
You didn't check?!
I remember seeing a green SSL icon.
Maybe they had one of those cheapo certificates, with minimal checks?
-
I'm wonder if they really meant that they're now using an Extended Validation SSL certificate.
-
Maybe it was like a Korean bank and using a custom system based on ActiveX.
-
This isn't a thing. The price of a certificate doesn't affect the security - while the validation measures differ (DV, OV, EV), it's unlikely that one would be spoofed. If someone has the ability to get certs for arbitrary domains, there are bigger issues afoot.
-
One of the banks I use (incidentally, one of the largest financial institutions in Europe) didn't use SSL by defaut on their login page until last year.
They had a nice EV certificate, and you could access the SSL version by clicking on a link or manually adding "https" to the URL, it just wasn't enabled by default.
Like I usually say, banks (and many other big corporations) live in a different world. They don't see security as their responsibility. It's the criminal's fault they broke in, not the bank's fault for being there! They'll use the legal system to put people in jail, and revert ilegitimate transactions, but will never take any preventive measures. Like in the physical world, where we don't blame people for having easy to pick locks because it doesn't really make a difference. That's why they sue people who report vulnerabilities.
-
This isn't a thing. The price of a certificate doesn't affect the security - while the validation measures differ (DV, OV, EV), it's unlikely that one would be spoofed. If someone has the ability to get certs for arbitrary domains, there are bigger issues afoot.
That's what I thought. They switched from a simple one, that just ensures secure communication, to one of those fancy ones for payment processors.
-
Like I usually say, banks (and many other big corporations) live in a different world. They don't see security as their responsibility. It's the criminal's fault they broke in, not the bank's fault for being there! They'll use the legal system to put people in jail, and revert ilegitimate transactions, but will never take any preventive measures. Like in the physical world, where we don't blame people for having easy to pick locks because it doesn't really make a difference. That's why they sue people who report vulnerabilities.
In a way, that would be how things worked in an ideal world.
That's, however, not the world we live in.
-
They don't see security as their responsibility. It's the criminal's fault they broke in, not the bank's fault for being there!
So the crazy rape people are taking cues from the banksters...
-
"banks ... live in a different world." I spent a number of years working in the IT security dept of a very large bank. They took security very, very seriously indeed. The role was in fact mainly policing the brain-dead internal business projects. I remember we killed several projects that had spent tens of thousands developing insecure apps and now wanted us to deliver a security "blessing".
On the other hand, while working for the service provider from hell, I discovered that one of our customers was running a little bank on a machine I could've picked up and carried out the door.
-
banks ... live in a different world
"Security" at a bank mostly consists of letting people break in and then filing legal charges against them. That doesn't work so well on the internet where the money can be sent to fifteen different countries before a minute has passed.
-
That doesn't work so well on the internet where the money can be sent to fifteen different countries before a minute has passed.
Well… theoretically. In practice, the actual transfers between banks (or different subsidiaries of the same bank) take rather longer than that. Until the criminal has actually got the money, i.e., cash, they're really vulnerable to the transaction being reversed.
projects that had spent tens of thousands developing insecure apps
Given how much developers cost, each of those is only going to be a month or two of effort, yes?

-
I use a Firefox browser extension called FORCE HTTPS along with SSleuth which ranks the SSL/TLS connection... If the site isn't using it by default, the browser tries to force an https connection and one can get certificate info, etc, from the address toolbar box.<center>
 </center>
</center>Works with FF64bit as well as 32bit..
Shy
-
Early part of third millennium. Microsloths 3 layer architecture. A lot of
VB, COM+ etc...The issue was that generally that external entities were supposed to
establish an encrypted link right through our firewalls. Ha Ha Ha! We'd
just point, laugh, and say WTF?The SYSTEMIC issue was that the project owners were able to put proposals
to management, get funds and do a whole lot of work when they had
completely missed the fact that the bank had a project management policy
that required IT Security and Corporate Risk to sign off before they
started work.
-
The issue was that generally that external entities were supposed to
establish an encrypted link right through our firewalls. Ha Ha Ha! We'd
just point, laugh, and say WTF?Using your COM objects directly from outside the organisation? As opposed to a service that can be exactly tracked and understood and managed? Shoot away!
-
COM+ was state-of-the-art in 2001.
At least it wasn't a proprietary
http://www.networkcomputing.com/careers-and-certifications/just-say-no-to-proprietary-cryptographic-algorithms/a/d-id/1230781?
solution.
-
Wait a sec. They just now added SSL!?
WHAT THE FUCK WERE THEY USING 'TILL NOW!?
I worked for a (very) large bank and that level of security awareness doesn't sound strange to me at all.
Oh, the things I saw and heard...
 Extended Validation Certificate - Wikipedia
Extended Validation Certificate - Wikipedia
