About that codepen fun
-
Continuing the discussion from Codepen fun:
Just sent a PM to 4 dev's rather than posting publicly.
I included a couple of sample URL's in the message....
you might also want to PM codepen that their service is a vector for XSS attacks?
502 bad gateway: GO AWAY! we don't want you! (x4)
403 Forbidden: IT WASN'T WHEN I FIRST TRIED TO POST HERE!
502 bad gateway (again): GO AWAY! we don't want you! (x5)
ten minutes later:
502 bad gateway (again): GO AWAY! we don't want you! (x2)
frackinghellfire! message-bus is working! WHY CAN I NOT JUST MAKE A POST?!
SO IS SAVING DRAFTS!
GAH!
502 bad gateway (again): GO AWAY! we don't want you! (x2)
-
Server cooties again I think - you're not the only one...
Apparently codepen was whitelisted...
Edit: Another one:
-
Server cooties again I think - you're not the only one...
i really think we're well beyond server cooties on that one.....
-
They've been pretty bad today.
-
Can't you just disable embedding this site?
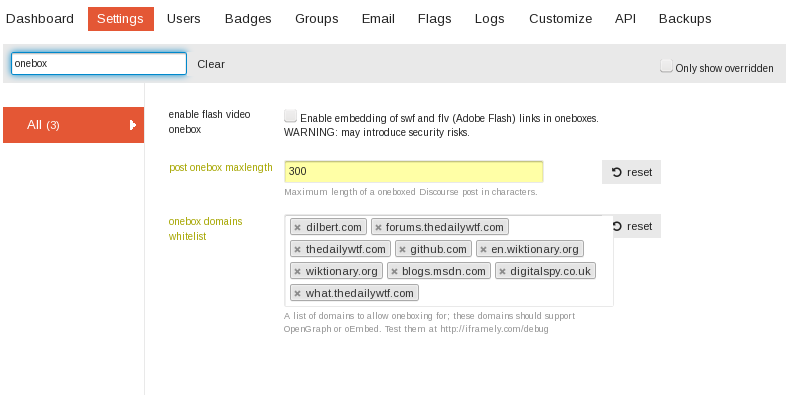
Nope (and there'd be uproar if I could, and did.) And I can't even blacklist the stock whitelisted ones - only add to it.
-
-
-
I don't see why there'd be uproar about blacklisting codepen. Seems pretty open and shut.
-
why is embedding SWF and FLV even an option?
-
don't see why there'd be uproar about blacklisting codepen. Seems pretty open and shut.
that one? no. but @pjh (and i think @Maciejasjmj) were talking about turning it off entirely.
and as @pjh explained we can't turn off codepen without taking an update because we can't remove default whitelisted sites.
-
Oh, yeah, turning off OneBoxing entirely would cause an uproar. Definitely.
-
I don't see why there'd be uproar about blacklisting codepen.
Uproar about disabling oneboxing. Altogether. All of it.
-
You were hanzoed by over 2 minutes.
-
roar Roar ROAR
-
-
I know - just making it clear.
-
Wonder how many more attack vectors they would have to block off from their built-in whitelist before they drop it altogether...
-
It's more authoritative when @PJH says it than when @accalia does. I just read "embedding this site" to mean "embedding codepen" instead of "embedding stuff on TDWTF."
YEMV.
-
Wonder how many more attack vectors they would have to block off from their built-in whitelist before they drop it altogether...
oh hellfire...... who chose what sites autoonebox?
because that list is at LEAST ten times longer than it should be (and that's being generous)
-
It's more authoritative when @PJH says it than when @accalia does
/me makes a note
"must... become... more... authoritative.... but... not... authoritarian.... remember... the difference."
-
I just read "embedding on this site" to mean "embedding codepen" instead of "embedding stuff on TDWTF."
I didn't even notice that the word 'on' was missing.
I think @Maciejasjmj did actually mean the single site concerned and I'm the one who misunderstood it....
-
I think @Maciejasjmj did actually mean the single site and I'm the one who misunderstood it....
That would be right, yes.
But the fact that you can't modify the whitelist is a WTF in and of itself...
-
I read it this way too.
edit: Hanzo
-
-
You can modify the list by adding to it as I understand it.
Not sure what a default system that you can't delete from is, though. Needs a better name.
Filed Under: DiscoDefault?
-
-
Speaking of which, I thought there was another site that was on the built-in whitelist that broke oneboxing, but I don't remember what it was or where it was posted, but I might be able to find it...
Edit: Found it. TechCrunch.
that list
Found here:
http://what.thedailywtf.com/t/scotusblog/1315/429?u=chaostheeternalAnd most likely is out of date (seeing as it's 6 months old). But, really, the default list should be much, much shorter.
-
Not sure what a default system that you can't delete from is, though. Needs a better name.
Well I've asked for a blacklist that can override the stock whitelist. (And suggested a site-wide switch for oneboxing.)
I'm not holding my breath for either.
-
I don't think a blacklist that overrides the whitelist sounds weird. While restricting should be prioritized what really bothers me about this is this:
So, let's say you program something like this. And you have a whitelist that you can edit (like you apparently do in your screenshot)... then why do you still need a hidden whitelist? Put them all out there! Be honest about what you allow to go through. I wouldn't want to check the Devs-Forum just to find out what Discourse allows but never states...
And if the list of whitelists gets bigger so what. Seperate them into "User Defined" and "Discourse Default" and put a freaking line in between. Done?!Addendum:
@loopback0 said:To the Discopaedia!
I'll let you have that one. I am too lazy to update that topic
-
I'm not holding my breath for either.
They're all about removing color in favor of black and white everywhere else. You'd think this'd be a slam dunk.
-
Speaking of which, I thought there was another site that was on the built-in whitelist that broke oneboxing,
[HA:pjh@sofa onebox]$ git log -p lib/onebox/engine/whitelisted_generic_onebox.rb | grep "\- [a-z]*\.[a-z]*$" - codepen.io - justin.tv - time.com - youtube.com - archive.org [HA:pjh@sofa onebox]$Of interest, found while figuring out the regex above:
[HA:pjh@sofa onebox]$ git log -p lib/onebox/engine/whitelisted_generic_onebox.rb | grep codepen Don't whitelist codepen by default. - codepen.io Whitelist codepen.io now that they support oembed! + codepen.io [HA:pjh@sofa onebox]$so it was actively added after the initial list.
-
-
-
But, really, the default list should
be much, much shorter.not exist in its current shape at allSeriously. For fuck's sake. They're hardcoding a whitelist of untrusted domains. If any of those domains goes AWOL for whatever reason, your forum is basically toast unless you disable all oneboxing until the developers come up with a fix or you tweak the source (which you can't do without server access, and can't do at all on a hosted instance they're selling).
Any exploit to be found on any on those sites can potentially be an exploit for Discourse.
-
unless you disable all oneboxing
I read
(And suggested a site-wide switch for oneboxing.)
as "You can't disable oneboxing
 "
"tweak the source
Isn't that one of the points the devs tried to sell Discourse with: That you could make your own branch if need arises.
Just to clarify: I completely agree with your statement that this is dumb and a potential attack vector and all....
Filed Under: Clarification should not be needed on this topic but meh!
Addendum: You have seen how much they blamed Google for Discourse running slow on android devices... what makes you think exploits on other sites are handled differently?
-
not exist in its current shape at all
I concur.
And most likely is out of date (seeing as it's 6 months old). But, really, the default list should be much, much shorter[b]<!--by being empty-->[/b].
Side note, I'm going to keep hidden comments to a minimum from now on.
Any exploit to be found on any on those sites can potentially be an exploit for Discourse.
Now you just need to convince them of that. Start getting more of those built-in whitelisted sites exploitable.
-
unless you disable all oneboxing
LOLWUT? Haven't we already covered this? Can't be done.

-
Well that's just even more fun, isn't it.
-
Haven't we already covered this? Can't be done.
Yes, we did, but I got the impression it was technically possible, but that you wanted to avoid being burned at the stake by us irate users.
-
That's idiotic.
-
Ya think?

-
Why is it that we still can't SECURELY embed arbitrary content in a web page? I thought HTML5 was supposed to fix that?
-
Why is it that we still can't SECURELY embed arbitrary content in a web page? I thought HTML5 was supposed to fix that?
Because Javascript.
-
Yet paradoxically, JavaScript is the most successful sandboxed language.
-
SECURELY
arbitrary content
Is there any achievable way to combine those two goals?
-
Is there any achievable way to combine those two goals?
sounds rather like an oxymoron to me. ;-)
-
If I'm using up to date Firefox or Chrome with plugins disabled, I feel confident enough to open and run any website you give me, so yes. It's putting that website inside another website that seems hard.
Also, consider this: virtual machines are as arbitrary as you can get, and large cloud providers (AWS) run millions of them so they must be pretty secure if they don't get all their servers rooted every week.
-
@anonymous234 said:
arbitrary content
Is there any achievable way to combine those two goals?It depends on what you mean by “arbitrary content”. ;) Specifically, you can take an arbitrary stream of bytes and have a reasonable chance of getting something that will not lead to any kind of attack on your system when you render them, provided you treat that stream of bytes as plain text in a suitable encoding. It might not be what the originator of the stream of bytes intended, but it is securely rendered.
[spoiler]Yes, I picked that encoding deliberately because it a reduced attack surface even by comparison with ASCII.[/spoiler]