I earned the sexy CSS award (also: Ask riking to fix stuff-topic!)
-
Awarded to finders of site-breaking exploits
(1) Logging in as system and (2) fixing the exploit. I think that counts.
awarded at admins' discretion
@system is an admin, so I think that counts.
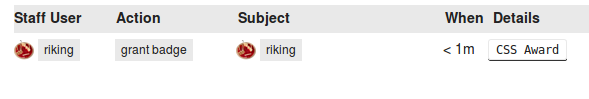
Proof:
Also note that I am not an admin (anymore), but I had to be to grant myself the badge.
-
Just for fun, I also gave it the long-name of 'systern'. Because @systern has a long-name of 'system'. Sadly, that seems to be erased every update.
-
-
It's the best how liking your post causes dicsourse to re-hide the content.
-
no, that was admin aboose trying to undo the admin aboose of hiding his post
-
It's even better that now that it's unflagged, it shows as un-liked by me as well. I guess I will like it again harder.
-
I should probably stop now
-
@system said:
no, that was admin aboose trying to undo the admin aboose of hiding his post
unless you were spamming the heck out of it, I reproduced it about 5 times with like & unlike & like & unlike & like.
-
it was worth posting that
-
Oh, that.
That's a bug with reloading a post - several things get reset that shouldn't be. Which happens when you like a post.
A possible fix would be to not reload the post if it was your like that triggered it. Except not really, because then someone else liking the post would trigger it.
-
A possible fix would be to not reload the post
if it was your like that triggered it. Except not really, because then someone else liking the post would trigger it.and instead update the pieces that actually changed.
FTFY
-
Transactional logic requires logic.
-
A possible fix would be to not reload the post and instead update the pieces that actually changed.
Well, yes, that's what the code CLAIMS that it does......
-
can we know how it was done?
-
Easy, he just logged in as System, who is an admin, gave himself the badge and then posted as system a few times in this topic.
Oh, you wanna know how he logged in as System? Since they probably fixed it in the latest version, couldn't you just look at the changes in the Source-Code to see what they changed?
Filed Under: Maybe he even used magic!
-
Since I assumed from his post that having admin privileges allowed him to fix the exploit, and none of the pull requests that have been merged or submitted make any reference to this, I don't think my question was unreasonable.
fuck you, no dinner plates for you.
-
Well, the main
emailthat the auth provider gets back from GitHub was the unverified, public, free-text-entryEmail (public)field.This was used to match the email against an existing user, and it would sign you in as that user if there was a match...
So I set my public, unverified, free-text-entry email to the email address that @system uses -
no_email.@PJH feel free to hit the "log out" button on /admin/users/system to trash the auth token
-
Meta was updated in the last 8 hours (during my sleep). This topic popped up during that timeframe. They would probably not publicly announce that they have an exploit that gives you admin rights if it wasn't fixed.
I come to the conclusion that the newest update fixed the problem.
Then again, I could see you coming to your conclusion, too. Seeing how the first post is phrased

Filed Under: You can have my plates! I am having my soup from a bowl anyway!
-
They would probably not publicly announce that they have an exploit that gives you admin rights if it wasn't fixed.
I actually used the exploit to perform the upgrade. wheeeeeeeeee
-
that's an impressively simple massive security breach.
now that I know that, I could have discovered it in the change log.
+1, would discourse again.
-
Twitter is not vulnerable, as it doesn't even give us any emails. Accounts with twitter auth have to have signed up with Twitter auth. (They can add the rest keyed on email.)
Facebook gives a valid email or no email.
Google OpenID (old) gives valid emails.
Google OAuth2 tells us whether the email is valid.
Yahoo gives valid emails.
I would hope that any official-e-z-SSO provider would have a unique index on the email column. (If SSO is used, it is the only signin path. Example: http://talk.openmrs.org/ )Only Github logins had this problem.
-
Did you know you can show a badge besides your username in your posts? You should totally try it out because giving yourself an exploit badge and not showing it off is clearly doing it wrongtm
Filed Under: Don't make me find an exploit to sign in as you just to set that badge! | Explaining unnecessary things to devs (who know them anyway) is the best activity early in the morning!
-
I went to a lot of trouble to type that in. Every time I went back to edit it, the entities
<turned back into actual<s.Happy?
-
I see Discoursistency is alive and well since in posts if I want a < I have to damn well write my own entity for it.
-
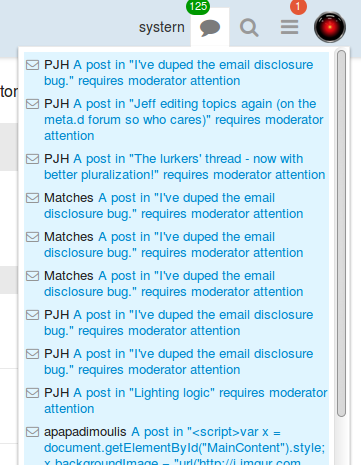
Next up on the chopping block, "view older notifications..." not actually showing you notifications.
-
please fix that.
I rage pretty hard every time I go to sleep and everyone gives me mad love and I can only see the last few mad loves.
-
Did you also see the topic of hilarity where we were going back on the activity page to see how far back we could go before we crashed our browsers? Firefox didn't even make it to '3 days ago' when I tried...
-
Yeah, I'm going to test out how it does here to stress-test my hypothesis that
{{#each}}correctly handles adding new things, as opposed to{{#groupedEach}}(used on the activity page) rebuilding the entire fucking thing every time. (Yes, with string concatenation as someone mentioned.)BTW it will load in chunks of 60
-
I'd say: close enough
I updated the title to reflect the current situation, though. Otherwise it's a barrier to dump work on you!
Filed Under: I also added some word that your old title was lacking. You can thank me later!
-
My activity profile is a great stress test for this

-
Well, until we get the magical 'local js app, remote server' setup happening that wouldn't help until it gets deployed.
-
Aside of proposing 27 different centralized login solutions without fully understanding how they work, I think TRWTF is that Discourse allows logging in to the @system account (especially since its email address is public and not randomized).
That got me thinking... Does @system has a password? It’s probably randomized on install, but maybe it’s discoverable...
-
The password field is null.
-
how does ruby deal with null == null?
if we manage to post a request such that password evaluates to null, will we login to system successfully?
-
The password field is null.
I hope nobody runs Discourse on an Oracle database...
(Yes, I know it wouldn’t work)
-
-
Next up on the chopping block, "view older notifications..." not actually showing you notifications.
yes.
-
oh wait, i thought you meant you were going to make the page actually show more notifications, not just fix the current broken list of a bunch of random crap to not crash your browser. :sad_face: The current "All" list is so useless that no one even noticed it breaks your browser for over a year....
unless, if that was just an interim fix for low-hanging fruit, then carry on sir.
-
Ruby doesn't have null, it has nil. (I meant NULL in the database.)
Unlike Java, you can call methods on nil. So comparison does just fine.
[1] pry(main)> a = nil => nil [2] pry(main)> a.class => NilClass [3] pry(main)> a.nil? # this is a method defined in NilClass => true [4] pry(main)> a == 2 => false [5] pry(main)> a.==(2) # in ruby, == is a method => false [6] pry(main)> a.to_a #to_array => [] [7] pry(main)> a.to_c #to_complex => (0+0i) [8] pry(main)> a.to_f #to_float => 0.0 [9] pry(main)> a.to_h #to_hash => {} [10] pry(main)> a.to_i #to_integer => 0 [11] pry(main)> a.to_r #to_rational => (0/1) [12] pry(main)> a.to_s #to_string => "" [13] pry(main)>
-
Not to forget, nil and false are the only falsy values in the entire language.
Which allows you to use || for nil checking.
-
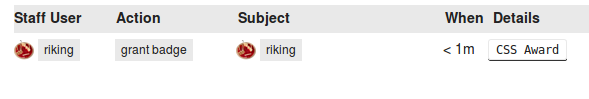
Did I miss the part where someone got an XSS award for reporting this, or am I the first to notice that there is an XSS vulnerability in the Details column of that table?
-
Does it count as an xss if you have to be an administrator to create the badge?
Seems more like a wontfix;asdesigned type of thing.
-
This is a debate I have had numerous times with 'security researchers'.
-
It's an actual tricky question. I would lean in this case to say that it is a bug, since moderator level people can create XSS accidentally/on purpose, where that type of power really should lie with rootadmin.
But it's one of those areas that's very grey depending on your software. Badges are an interesting area, because they are fully customizable, and if you remove XSS potential, you also restrict what can be done with badges (for good or ill)
-
You know where I've had that debate before.
In this case it is always areas the admin (and only the admin) has access to in the first place.
What kills me is that they complain about certain things as exploits but pretend to ignore the fact that the theme editor (that lets you edit the raw PHP of the theme files) is not a vulnerability even though it can be exploited exactly the same way by design. Or for that matter the package manager which lets you upload chunks of raw PHP complete with find/replace on the master files. But these aren't considered vulnerabilities...
-
Yeah, just a few pages over there's a box that lets you enter raw html to be put in the
<head>for all users.It doesn't seem like there's any other spot that a badge name is spit out unsanitized.
In fact, that section is outputting HTML by design. Which is a little weird. The logs are supposed to contain HTML there. Which is again weird.
That raw html section includes suspension messages. So, if you put HTML in a suspension message, it will be escaped everywhere except for that screen.
On a side note, I cannot find where the
{{#grouped-each}}has the performance loss that I thought existed compared to plain{{#each}}. So, that may be out the window (on the user stream).
-
Did I miss the part where someone got an XSS award for reporting this, or am I the first to notice that there is an XSS vulnerability in the Details column of that table?
Ohh. Well spotted... (though given that image is from the admin section I presume it's effect is on a par with it happening when I got mine - only admins can create the content concerned...)
@sam, @riking. XSS clean-up in aisle 9? (The post above not-withstanding...)
-
Indeed. I'd say it's still a vulnerability since it could be used by one mod/admin against another. Since the original XSS issue with badges was cleaned up, this should be too.
@PJH XSS Award partial credit?

Filed under: Goddamnit these new emojis are even creepier than the old ones.
-
@PJH XSS Award partial credit?
I'm just waiting for an acknowledgement, or otherwise, that it is in fact XSS.
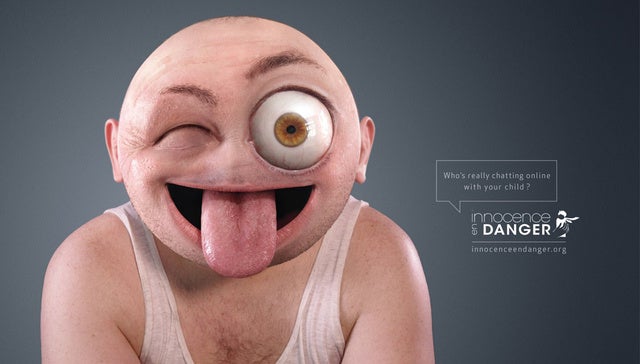
Goddamnit these new emojis are even creepier than the old ones.
Be glad they only did 3 of these:
That I could find...
-
Be glad they only did 3 of these:
Doing 3 of those: bad idea
Not doing 4 of those: good idea