Information security
-
Information security mandatory online training. This should be fun:
[on commonly used terms]
The media is a good place to pick up on these, as Information Security crimes have become increasingly common
Yes, because the Media always reports computer based stuff without mangling it beyond recognition...
Cybercrime is a term we hear more often these days and is a bigger risk than ever before due to the large number of connected people and devices. Basically it's a crime that involves some kind of computing device and has a cyber aspect to it, such as the internet.
oooh, a cyber aspect. Nifty
Quick question: Which do you think is a bigger problem today, Cybercrime or Illegal Drug Trafficking?
- Cybercrime
- Illegal Drug Trafficking
It doesn't define "bigger problem", but apparently cyber crime brings in more money than drug dealing. Bloody druggies, sitting on their arses while the geeks do the real work
A hacker can mean many things such as a person who 'hacks' to improve things or an expert at programming and solving problems with a computer.
However, it can also be used to describe a person who illegally gains access to a computer system to obtain information or cause malicious damage.
That's actually not an awful description. I like that it mentions the old definition of hacking
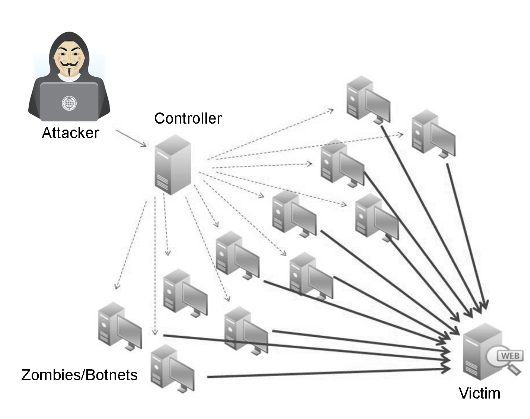
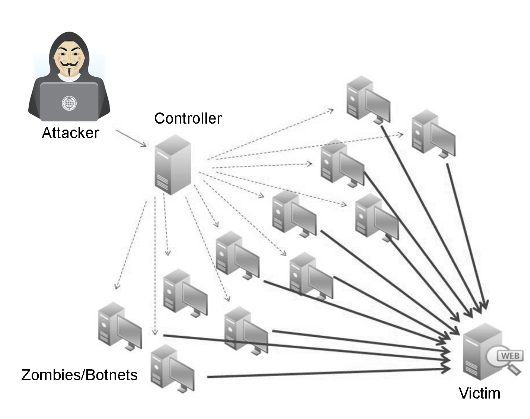
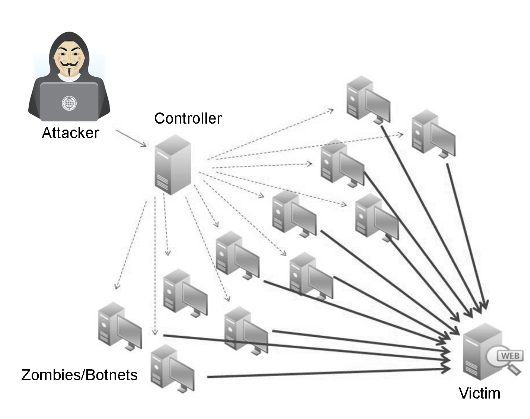
Over the last few years, DDOS attacks have increased in frequency and size. Gaming services such as Microsoft XBOX Live and Sony PSN Networks are regularly targeted along with other popular services such as Blizzardbattle.net
I hate it when blizzardbattle goes down
Is he wearing a mask so his laptop's webcam can't identify him?
A threat can be defined as anything that is capable of causing harm. A person driving a car is a threat, as is a hacker, a cybercriminal or a severe storm or flood.
If an employee perceives a threat then they need to report this to their Line Manager, Service Desk or the Information Security Team.
Should I report every car in the car park?
That's module 1 of 3. Unlike previous courses I couldn't go straight to the quiz without reading the modules.
I'll post some stuff about the others when I get round to them
-
@Jaloopa said in Information security:
a cyber aspect.
ooooh. it's been ages since i've had a good cyber
 session.
session.yeah, that sounds like it could be fun.
-accalia winks suggestively at @ajaloopa-
-
@accalia I take off my robe and wizard hat
-
@Jaloopa said in Information security:
@accalia I take off my robe and wizard hat
-accalia likes what she sees-
-
@Jaloopa said in Information security:
Should I report every car in the car park?
Only when a person is driving it:
@Jaloopa said in Information security:
A person driving a car is a threat,
-
@boomzilla said in Information security:
@Jaloopa said in Information security:
Should I report every car in the car park?
Only when a person is driving it:
@Jaloopa said in Information security:A person driving a car is a threat,
Yes, the person driving it is a threat to global climate. They should be taking the
 to work, instead.
to work, instead. 




 :)
:)
-
@Jaloopa said in Information security:
Is he wearing a mask so his laptop's webcam can't identify him?
Did you know? All criminals dress in dark-colored hoodies at all times!
-
-
@Tsaukpaetra and they all look like a stylised Guy Fawkes figure from the 1980s. It's literally only the guy, but with his mad cyberhaxx0rz skillz, he's everywhere.
-
@clatter so much for his multiple successful businesses. He's just installing botnets at all his client sites
-
@Jaloopa said in Information security:
It doesn't define "bigger problem", but apparently cyber crime brings in more money than drug dealing. Bloody druggies, sitting on their arses while the geeks do the real work
What about cyber criminals running a drug-trafficking website?
-
@accalia said in Information security:
ooooh. it's been ages since i've had a good cyber
 session.
session.:/
o baby I'll flack your bran out.
-
@Lorne-Kates said in Information security:
@accalia said in Information security:
ooooh. it's been ages since i've had a good cyber
 session.
session.:/
o baby I'll flack your bran out.
finger me for my ICQ handle. call me and we'll cyber all night darling.
-
-
@No_1 said in Information security:
@accalia said in Information security:
finger me

Filed under: Way too easy to ignore
@No_1
 @accalia better than this!
@accalia better than this!No, wait, that's a lie....
-
@Jaloopa said in Information security:
That's module 1 of 3. Unlike previous courses I couldn't go straight to the quiz without reading the modules.
This is basically one of the only good things about this course, from what you've posted. Who is providing this course?
-
@No_1 said in Information security:
@accalia said in Information security:
finger me

Filed under: Way too easy to ignore
-
@Arantor said in Information security:
@Tsaukpaetra and they all look like a stylised Guy Fawkes figure from the 1980s. It's literally only the guy, but with his mad cyberhaxx0rz skillz, he's everywhere.
Who is this infamous hacker Mallory and why is he always trying to attack Alice and her husband, Bob?
-
@Sumireko said in Information security:
Who is this infamous hacker Mallory
Sterling Malory Archer, of course. Season 7 plot revealed!
-
@Fox said in Information security:
@Sumireko said in Information security:
Who is this infamous hacker Mallory
Sterling Malory Archer, of course. Season 7 plot revealed!
TONIGHT on "Blonde chick hacks some things and goes through relationships with a (side) of superheroes":
https://i.imgur.com/jc8Zmjd.jpg
Context for those not in the Arrow know: a once great superhero show was ruined by several plots/subplots involving romance between Byvire naq Sryvpvgl [ROT13], and episodes quickly became contingent on Sryvpvgl [ROT13] hacking one thing or another
-
@Sumireko said in Information security:
Pbagrkg sbe gubfr abg va gur Neebj xabj: n bapr terng fhcreureb fubj jnf ehvarq ol frireny cybgf/fhocybgf vaibyivat ebznapr orgjrra Byvire naq Sryvpvgl [EBG13], naq rcvfbqrf dhvpxyl orpnzr pbagvatrag ba Sryvpvgl [EBG13] unpxvat bar guvat be nabgure
Vs lbh fnl fb...
-
@ben_lubar said in Information security:
@Sumireko said in Information security:
Pbagrkg sbe gubfr abg va gur Neebj xabj: n bapr terng fhcreureb fubj jnf ehvarq ol frireny cybgf/fhocybgf vaibyivat ebznapr orgjrra Byvire naq Sryvpvgl [EBG13], naq rcvfbqrf dhvpxyl orpnzr pbagvatrag ba Sryvpvgl [EBG13] unpxvat bar guvat be nabgure
Vs lbh fnl fb...
Dammit, we told you we don't know Lojban.
-
@Maciejasjmj said in Information security:
@ben_lubar said in Information security:
@Sumireko said in Information security:
Pbagrkg sbe gubfr abg va gur Neebj xabj: n bapr terng fhcreureb fubj jnf ehvarq ol frireny cybgf/fhocybgf vaibyivat ebznapr orgjrra Byvire naq Sryvpvgl [EBG13], naq rcvfbqrf dhvpxyl orpnzr pbagvatrag ba Sryvpvgl [EBG13] unpxvat bar guvat be nabgure
Vs lbh fnl fb...
Dammit, we told you we don't know Lojban.
Apparently rot13 is so important to the lojban community that they put a dedicated bot for it in their channel.
-
@ben_lubar said in Information security:
rot13
Challenge! A rot13adrome.
A word that, when rot13'd then spelled backwards, spells the same word.
Go.
-
@Lorne-Kates
comm -12 <(sort /usr/share/dict/american-english) <(tr a-zA-Z n-za-mN-ZA-M < /usr/share/dict/american-english | rev | sort)
-
ravine <-> ravine
labor <-> ebony
leers <-> ferry
liar <-> envy
-
@Lorne-Kates said in Information security:
@ben_lubar said in Information security:
rot13
Challenge! A rot13adrome.
A word that, when rot13'd then spelled backwards, spells the same word.
Go.
Mmmmmmm
-
@Fox said in Information security:
@Jaloopa said in Information security:
That's module 1 of 3. Unlike previous courses I couldn't go straight to the quiz without reading the modules.
This is basically one of the only good things about this course, from what you've posted. Who is providing this course?
It's an internal thing. Sometimes they try to make it fun, like the "Knights of [my company]" for some other security thing.
Before this, mostly, the main page has had all of the modules and the final test selectable, so it was possible to just go to the test and answer the (usually trivial*) questions to get the required pass
*e.g. "You see someone without an ID badge who you don't recognise rooting through a filing cabinet. Do you a) offer to help, b) ask to see their ID, c) shoot them?
-
@Jaloopa said in Information security:
"You see someone without an ID badge who you don't recognise rooting through a filing cabinet. Do you a) offer to help, b) ask to see their ID, c) shoot them?
It depends. Is this America?

-
Module 2:
[Company] considers the security of our business, employees and our customers information to be of the highest importance.
I'm guessing it's given exactly as much importance as regulations say it has to.
It is also a regulatory requirement for us to have good, stringent Information Security practices in place to ensure the safety and security of our systems and information.
Called it!
We will often conduct audits and checks on our clients and 3rd parties businesses to verify that they provide the necessary level of Information Security, and they also do the same to us.
Except the provider who was developing the project I'm now on, with plaintext passwords stored alongside an unused salt?
There are a number of negative implications for our business not getting Information Security right. These include:
•Disruption to our systems and to the availability of information - which may partially or completely interrupt our normal business processes•Increased regulatory scrutiny - the FCA can visit and/or audit us at any time, but may choose to do so particularly following a breach
•Fines or penalties may be imposed - leading to poor financial results for our business
•Embarrassment and damage to our reputation - which may deter current or potential policyholders, suppliers, partners, brokers, intermediaries and other third parties from dealing with us now or in the future
Just as there are negative consequences of getting information security wrong, similarly there are a number of benefits when we adopt good practices. These include:
•Customer, employee and company information is protected from attack and misuse•We avoid bad publicity
•Our regulators are happy and we avoid enforcement action
•Improved customer service and increased customer confidence in us
•Our productivity is maintained (or even increased)
•The risk of financial loss is minimised
Good things appear to be mainly that bad things don't happen
Remember, we all have a role to play!
Robe, wizard hat etc.
Specific responsibilities:
IT:
•They ensure that all staff have the correct permissions and access to the information they need to do their job
No real distinction between IT and development. Pretty sure this isn't my problem
•Facilities are responsible for all aspects of Physical Security including door access control systems, building security, CCTV, fire detection etc.
that's not information security
•The L&D team will ensure that Information Security Training is delivered to all staff when they join the business, and then on an annual basis as a refresher
good for them.
Periodically, the policies will be updated to reflect changes in the way the business operates and it is essential that you set time aside throughout the year to keep up to date with these changes.
Yeah, I'll definitely do that.
-
@thegoryone said in Information security:
3rd party penetration tests that highlights IIS vulnerabilities on Ubuntu machines running Apache
Ho ho!
-
@thegoryone We had a pen test recently. Helpdesk weren't told about it so when a site I maintain started spewing out a load of "potentially unsafe request" error logs I got lumped with the ticket. At least it was an easy one to solve
-
Section 3:
In this module we will explore real world examples of how our systems could be compromised and how to protect against them.
You will be taken through a fictitious scenario with situations that will bring to life the concepts being presentedThis should be fun
Welcome my brothers and sisters...
...we are [a bad pun based on the company's name and anonymous]...
...it is time for us to show you what we hackers can do if we are feeling particularly 'playful' and we're choosing you as our adversary...
...your actions will speak louder than words, therefore we have prepared a series of challenges for you which you will need to complete...
They always try to be fun...
You have found a USB device in the carpark, do you...
...plug it into your computer to look at the contents to see if you can return it to someone?
...report it to your local authority or the security team at work?
...give it to your neighbour to look at because he knows something about computers. At least then you're not plugging it in at work right?
This is literally the same page as it talks about USB drops and not to put them in your computer.
You have a confidential report that you really wanted to finish today but it's already 5pm and you really need to head home. Do you...
...take a printed version home, you won't let it out of your sight and you can type up your notes tomorrow. Incorrect option
...email it home and work on it this evening. You can always delete it from your computer after you email it back to work. Incorrect option
...admit defeat. Go home, enjoy your evening and work on the document in work tomorrow
Go home. The answer is always to go home
You receive a call from Tim, he says he's new to the Pay and Reward team. As its his first day, Tim says he doesn't have access to his emails or phone log in yet but he really wants to get started on some bonus processing. He asks you to send details for everyone in your area, along with their salaries, to his personal email so he can get started. He says your help will mean there is no delay to people getting paid?
Welcome Tim warmly to the company and send him what he needs.
Tell Tim you can't email it but if he meets you in the breakout area you'll print out what he needs and pass this to him.
Tell Tim that you cannot fulfil his request and then report his details to the Information Security team
I don't even know anyone else's salaries
Yesterday, I was looking at this one woman who was sat next to me on the train. She was happily using her laptop without any screen filters and I could clearly see her name on an email. Two minutes on Facebook and I had her workplace details, all her photos, family and friend details, likes, dislikes, location info, even the school her kids attended. Even better it turns out she uses Twitter and LinkedIn which were hacked a while ago. Never even changed her password, think I'll log into her account and keep an eye on her as her identity might come in handy very soon for some very expensive purchases.
Good job I don't put most of that stuff on Facebook
If you have been a victim of cybercrime, want to share your story or want to know more about how you can protect yourself, contact the Information Security Team on [redacted] and you can speak to someone in confidence who will assist you. You can also visit their page on the intranet
Share my story? Of not being a blathering idiot?
-
@Jaloopa quoted in Information security:
You receive a call from Tim
I scream at being startled like that. Nobody phones me! The phone is the devil machine!
Though I suppose you could instead start by asking him what he is wearing…(Also, all our phones are set to use a different ring with an external call to an internal one.)
-
@Jaloopa said in Information security:
"You see someone without an ID badge who you don't recognise rooting through a filing cabinet. Do you a) offer to help, b) ask to see their ID, c) shoot them?
All three, in the reverse order you listed them. Shoot first, look for ID badge, and offer to help once you find it.
-
@Jaloopa said in Information security:
*e.g. "You see someone without an ID badge who you don't recognise rooting through a filing cabinet. Do you a) offer to help, b) ask to see their ID, c) shoot them?
I once worked at a place where everyone in the building (except visiting politicians and other scum who came in occasionally to give TV and radio interviews, and probably people like Russell Crowe when he came to shoot parts of a film in our offices) had to wear a badge of some sort at all times while in the office. Numerous people were escorted back to their desks from the coffee-and-snacks area by the security guys, having left their badges behind. Very few people did it more than once, and I don't recall ever seeing it happen three times to the same person.
(EDIT: never happened three times, sometimes twice)
-
@Steve_The_Cynic
Probably because the second time, security escorted them to their desk and then the parking lot.
-
@izzion the security certifications ask for these things, but I never seen a place take it to this extreme
-
@Sumireko said in Information security:
Context for those not in the Arrow know: a once great superhero
showwas ruined byseveral plots/subplots involving romancebad writing that turned him into a bad Bruce Wayne knockoff from the very beginning, and Felicity was pretty much the only good thing in the entire show, until The Flash came alongFTFY
-
@Jaloopa said in Information security:
Is he wearing a mask so his laptop's webcam can't identify him?
My guess is they picked that image because of:
-
@Jaloopa said in Information security:
[Company] considers the security of our business, employees and our customers information to be of the highest importance.
I'm guessing it's given exactly as much importance as regulations say it has to.
Oh fuck, this course was made in-house by your company?
-
@Gurth said in Information security:
@Jaloopa said in Information security:
Is he wearing a mask so his laptop's webcam can't identify him?
My guess is they picked that image because of:
OOOOOOORRRRR they both picked that image because of
http://thelastgreatstand.com/wp-content/uploads/2016/08/Anonymous-2.jpg
-
@Jaloopa I swear, every company can just replace that part of their security training with "Here's a company iphone. Go play Mr Robot."
-
@Jaloopa Most of that stuff seems pretty reasonable. The point of this sort of training is to drive home good practices, not challenge your intellect or whatever.
I can assure you that I've taken so much more of this than you have. I am required to take multiple similar things every year. And while to a certain extent, I want to gag myself, too, it's still good to get refreshers on this sort of stuff.
OTOH, I also had to take some "active shooter" training recently and I learned some interesting things about dealing with sucking chest wounds, so you never know!
-
@boomzilla yeah, it was actually a lot better than I was expecting. We're not a tech company so it was mostly aimed at the less technical people
-
@izzion ... or possibly to the large quicklime pit on the back yard.
-
-
@Jaloopa said in Information security:
stored alongside an unused salt?
That's almost as bad as:
SELECT COUNT(distinct salt) FROM users; > results: 1
-
@Jaloopa said in Information security:
If you have been a victim of cybercrime, want to share your story
If you have been the victim of a cybercrime, please contact us and we will help you with your credit card plz include credit card number for your protection.
-
@RandomStranger said in Information security:
@izzion ... or possibly to the large quicklime pit on the back yard.
HEY, that's for personal use. If you want me to have a company quicklime pit, then pay me to have a separate one. I don't want my personal bodydumps getting mixed up with company bodydumps.
This is why we can't have nice things on Facebook.