PhpMyAdmin Project Successfully Completes Security Audit
-
Does anyone else think that if they haven't found major WTF they didn't look hard enough?
-
@marczellm well, it's a web application designed to make SQL injection easy.
One of the most common security flaws is actually intentional. That puts it ahead already!
-
So, what, should I update my copy? It's about six years out of date...
-
I replaced that sprawling mass o files with Adminer and never looked back.
Edit: congrats to phpMyAdmin, didn't want to detract or anything.
-
@marczellm said in PhpMyAdmin Project Successfully Completes Security Audit:
Does anyone else think that if they haven't found major WTF they didn't look hard enough?
It's probably technically secure, in that it now resists attacks by unauthenticated users correctly, but it's doing stuff by design and purpose that shouldn't be done without being highly authenticated. Someone who breaks in (e.g., by stealing a password, which no audit of phpMyAdmin will be able to help with) will be able to do great mischief.
Security audits help a lot, but they're just one tool and they don't prove the correctness of the overall system. Security is a global property of a system (everything is only as good as its weakest link) and all global properties are horrible to work with. Correctness is another such (and is unsurprisingly quite closely related).
-
@marczellm I choose to read "PhpMyAdmin Project Successfully Completes Security Audit" as "we initiated an audit successfully, and carried it to completely successfully". Note there's nothing that says the audit found no issues.
-
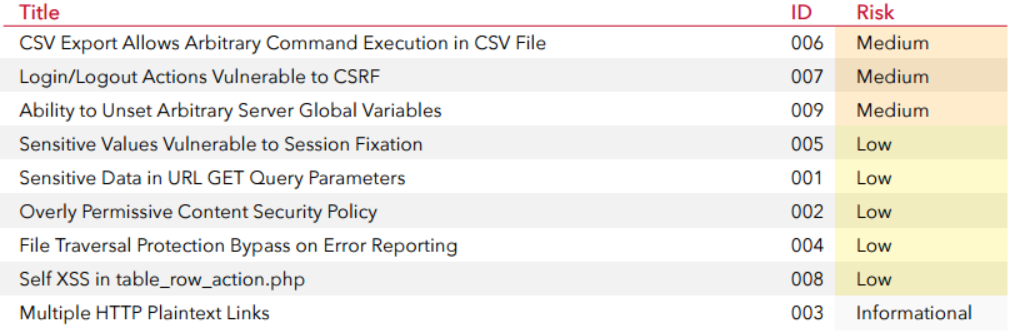
@FrostCat They found a few, although I'm not in a position to judge how important they are:
-
@dkf said in PhpMyAdmin Project Successfully Completes Security Audit:
by stealing a password
Why?
foreach(host in AllWebsitesOnTheInternet) { ConnectToPHPMyAdminDefaultPort(host); if(SendDefaultLoginCredentialsThatDumbshitsNeverChanged(host)) { PwdSite(host); } }
-
@FrostCat said in PhpMyAdmin Project Successfully Completes Security Audit:
@marczellm I choose to read "PhpMyAdmin Project Successfully Completes Security Audit" as "we initiated an audit successfully, and carried it to completely successfully". Note there's nothing that says the audit found no issues.
phpMyAdmin.
Release 1998.
Completed a security audit 2016.
-
@Lorne-Kates said in PhpMyAdmin Project Successfully Completes Security Audit:
DefaultLoginCredentialsThatDumbshitsNeverChanged
No such thing, at least when installing it using a package manager on Linux - is asks for a password during install, no defaults set.
That doesn't stop idiots choosing idiotic passwords, of course.
-
@dkf said in PhpMyAdmin Project Successfully Completes Security Audit:
It's probably technically secure, in that it now resists attacks by unauthenticated users correctly, but it's doing stuff by design and purpose that shouldn't be done without being highly authenticated. Someone who breaks in (e.g., by stealing a password, which no audit of phpMyAdmin will be able to help with) will be able to do great mischief.
I suppose PhpMyAdmin might increase the exposure to password theft a bit, but it's just a layer on top of the database password...that would give any hacker the same rights to destroy the database. Having a password for PhpMyAdmin stolen is no worse than having your password stolen when you have rights to sudo.
-
How difficult is it to make a 100% login walled site secure?
You have one vector of attack. You make the login workflow using best practices, and serve it through https. Done and done.
The way things like wordpress get into trouble is they allow mixed anonymous and walled access, and then on top of that, allow uploads. Much wider attack surface than php admin.
-
The problem with PhpMyAdmin, and any other similar Product in any language, is that it is free and open source. All you need to do is obtain a copy and search for weaknesses you can exploit. I think I've mentioned this before, but when I was running a LAMP Stack, every time there was a update I experienced a flurry of hack attempts.
It was not just a password issue, the attempts would be to try and run the "admin" scripts directly. Because you know where they are and what they do. So the trick is to not make it obvious you are using PHP and to not install to default directories.
-
@loose said in PhpMyAdmin Project Successfully Completes Security Audit:
It was not just a password issue, the attempts would be to try and run the "admin" scripts directly. Because you know where they are and what they do. So the trick is to not make it obvious you are using PHP and to not install to default directories.
You need a modern framework that uses a front-controller, instead of that shit with million little php files anyone can launch if they know where they are.
-
I used to run phpMyAdmin on my NAS, but I added some custom .htaccess to keep it from being served to the outside world. It might still be there.
-
@loose said in PhpMyAdmin Project Successfully Completes Security Audit:
All you need to do is obtain a copy and search for weaknesses you can exploit.
Some would say that's one of the strengths...
But I'm not interested in starting a flame war here....
-
@loose said in PhpMyAdmin Project Successfully Completes Security Audit:
It was not just a password issue, the attempts would be to try and run the "admin" scripts directly. Because you know where they are and what they do.
I've seen a number of (for example) Movable Type blogs that renamed the comment submission page to break hack attempts like that.
-
@Onyx said in PhpMyAdmin Project Successfully Completes Security Audit:
@Lorne-Kates said in PhpMyAdmin Project Successfully Completes Security Audit:
DefaultLoginCredentialsThatDumbshitsNeverChanged
No such thing, at least when installing it using a package manager on Linux - is asks for a password during install, no defaults set.
That doesn't stop idiots choosing idiotic passwords, of course.
Ah, there's your mistake. You're assuming an up-to-date (or even recent) install of phpMyAdmin-- and not just one that came pre-installed with someone's "Wordpress In A Box" package that they downloaded from a five year old link from Stack Overflow.
Or just a copy of phpMyAdmin that's been sitting on a server for eight years that no one even knew was there.
-
@Lorne-Kates said in PhpMyAdmin Project Successfully Completes Security Audit:
just a copy of phpMyAdmin that's been sitting on a server for eight years that no one even knew was there.

walks away to remove an otherwise innocuous folder...
-
@cartman82 said in PhpMyAdmin Project Successfully Completes Security Audit:
How difficult is it to make a 100% login walled site secure?
Very, apparently. There are plenty of pages that are vulnerable to command injection before authentication occurs.
The most basic could be:
page.php
<?php if(db_exec("select requires_login from WebPages where id=" & $_REQUEST("page_id") & ";") == true && IsNotLoggedIn()) { redirect("login.php"); } ?>
-
@Lorne-Kates The string concatenation operator is
., not&.
-
@asdf said in PhpMyAdmin Project Successfully Completes Security Audit:
@Lorne-Kates The string concatenation operator is
., not&.PHP is full of bugs.
-
@Lorne-Kates said in PhpMyAdmin Project Successfully Completes Security Audit:
@asdf said in PhpMyAdmin Project Successfully Completes Security Audit:
@Lorne-Kates The string concatenation operator is
., not&.PHP is full of bugs.
At least it's not full of stars...
-
@Tsaukpaetra said in PhpMyAdmin Project Successfully Completes Security Audit:
@Lorne-Kates said in PhpMyAdmin Project Successfully Completes Security Audit:
@asdf said in PhpMyAdmin Project Successfully Completes Security Audit:
@Lorne-Kates The string concatenation operator is
., not&.PHP is full of bugs.
At least it's not full of stars...
php_real_escape_starhole
-
@Tsaukpaetra said in PhpMyAdmin Project Successfully Completes Security Audit:
@Lorne-Kates said in PhpMyAdmin Project Successfully Completes Security Audit:
@asdf said in PhpMyAdmin Project Successfully Completes Security Audit:
@Lorne-Kates The string concatenation operator is
., not&.PHP is full of bugs.
At least it's not full of stars...
-
@marczellm it's very rare on TDWTF forums to see a thread title that makes it immediately obvious where the WTF happened, what it is, how big it is, and why exactly is it a wtf.
this thread was one of those rare cases.
-
@Lorne-Kates said in PhpMyAdmin Project Successfully Completes Security Audit:
PHP is full of bugs
php is dark and full of terrors
-
The first line in any of my PHP scripts is include_once(site_initialisation_script). This is the script that checks that the User is authorised and or part of a valid current session. If not, it does not redirect but includes the appropriate validation.
Int the case of third party scripts PHP has a nice little feature called auto pre-pend whereby a designated script is run before anything else. You can put lots of nice (or nasty) things in there that you now will be executed. It also has a similar auto append where you can ensure that certain things are always "cleaned up"
-
@loose said in PhpMyAdmin Project Successfully Completes Security Audit:
The first line in any of my PHP scripts is include_once(site_initialisation_script). This is the script that checks that the User is authorised and or part of a valid current session. If not, it does not redirect but includes the appropriate validation.
Assuming the authorization code doesn't have a vulnerability.
Also assuming the login page doesn't have a vulnerability.
-
@Lorne-Kates said in PhpMyAdmin Project Successfully Completes Security Audit:
Assuming the authorization code doesn't have a vulnerability.
Also assuming the login page doesn't have a vulnerability.Those are the bits you audit very carefully. Same as with any other web code; stuff that is meant to be run pre-auth needs to be hardened. (Post-auth depends on the profile of your users and what you're doing.)
-
@Lorne-Kates said in PhpMyAdmin Project Successfully Completes Security Audit:
Also assuming the login page doesn't have a vulnerability.
a secure login is a rare thing, because it needs several GiB of memory on the client machine