Arbitrary code execution: Package Manager edition
-
So some researcher just published a document about typosquatting on popular package managers.
The basic idea is, Python's
pip, Ruby'sgemand Node'snpmeach have some facility by which a package's author can cause the package manager to automatically execute arbitrary code on setup, and allow packages with arbitrary names to be uploaded with no manual oversight or code review. This is a beautiful combination for would-be botnet builders: just create a malicious package whose name is an easy typo version of a popular package.He uploaded a few hundred packages as a test, with arbitrary code that causes them to call home to a server he runs to gather statistical information, then published his results: over 17,000 computers "compromised" over the course of just a few weeks...
-
go getdoes not have this vulnerability.
-
@ben_lubar said in Arbitrary code execution: Package Manager edition:
go getdoes not have this vulnerability.yes, but then you have go on you.....
-
@ben_lubar yeah, but would you want anything to do with a machine owned by someone who uses Go anyway?
-
This really isn't a vulnerability so much as a generalized phishing attack, which you also commonly see with big business/banks. IE: bank of america might have a phishing site like 'bankoamerica' or any variant. It gets put up on the web and randoms go there, maybe enter un/pw that attackers can now go to the real BOA and log in.
The small difference is that sites tend to get reported, and taken down with varying degrees of speed. Package managers really don't have any cleanup because there's really no authoritative manager to enforce rules / go after people in the courts.
tl;dr;
This exists everywhere, in every industry where people are relying on user input to get the right end product.
-
@Matches said in Arbitrary code execution: Package Manager edition:
This really isn't a vulnerability so much as a generalized phishing attack, which you also commonly see with big business/banks. IE: bank of america might have a phishing site like 'bankoamerica' or any variant. It gets put up on the web and randoms go there, maybe enter un/pw that attackers can now go to the real BOA and log in.
The small difference is that sites tend to get reported, and taken down with varying degrees of speed. Package managers really don't have any cleanup because there's really no authoritative manager to enforce rules / go after people in the courts.
tl;dr;
This exists everywhere, in every industry where people are relying on user input to get the right end product.
But if I went to bankoamerica, the website wouldn't be able to run arbitrary code on my computer with root privileges. I'd have a chance to notice that my password manager wasn't giving me any autocomplete suggestions and that it wasn't loaded through HTTPS before anything bad happened.
-
@ben_lubar The concept is that the intended use isn't happening, and a malicious one is occurring instead. If you went to 'bankoamerica' and it offered a desktop app / mobile app you could install, and you blindly installed it - it absolutely could run arbitrary code on your machine for as long as you have it installed for.
When you run a package manager, you are doing the equivalent of going to the hosts site, downloading an exe / msi (or w/e your poison is for packaged content) - you are trusting it to download JUST relevant files, and install ONLY safe content.
You, the end user, are explicitly saying 'Hey, give me this thing, I want it' - and the computer obliges, because it assumes you are not randomly requesting shit.
This is a problem between the keyboard and the chair in most cases, where digital signing can help - the publisher can tell you what the signature should be, and you should verify the signature before installing - but fuck that noise right? That's a hassle. I'll just take my chances by not having typos. By extension, if you ever copy the command from a tutorial site and run it without though you're trusting THAT person to not have typos, and only refer to safe packages.
-
@Onyx said in Arbitrary code execution: Package Manager edition:
@ben_lubar yeah, but would you want anything to do with a machine owned by someone who uses Go anyway?
His passwords are probably in Lojban.
-
@Matches said in Arbitrary code execution: Package Manager edition:
you should verify the signature before installing - but fuck that noise right? That's a hassle.
Like every time I connect to a new SSH server, and it prompts me if I want to trust "random hex string" key. "Uh. I... I don't know. Probably?"
@Matches said in Arbitrary code execution: Package Manager edition:
By extension, if you ever copy the command from a tutorial site and run it without though you're trusting THAT person to not have typos, and only refer to safe packages.
Not to mention the whole paste-jacking thing.
-
@error said in Arbitrary code execution: Package Manager edition:
@Matches said in Arbitrary code execution: Package Manager edition:
you should verify the signature before installing - but fuck that noise right? That's a hassle.
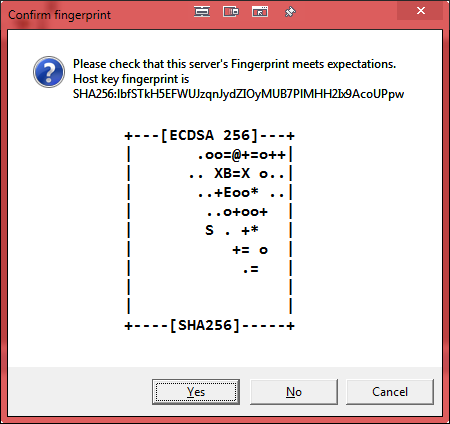
Like every time I connect to a new SSH server, and it prompts me if I want to trust "random hex string" key. "Uh. I... I don't know. Probably?"
The person who installed the cert that the SSH server is using should be able to tell you what the fingerprint (aka "random hex string") should be for it.
-
It should be relatively easy for the package manager to say "Are you sure you want to install this package with 6 downloads crated yesterday instead of that other one with 2,546,786 downloads created 12 years ago?"
-
@powerlord said in Arbitrary code execution: Package Manager edition:
@error said in Arbitrary code execution: Package Manager edition:
@Matches said in Arbitrary code execution: Package Manager edition:
you should verify the signature before installing - but fuck that noise right? That's a hassle.
Like every time I connect to a new SSH server, and it prompts me if I want to trust "random hex string" key. "Uh. I... I don't know. Probably?"
The person who installed the cert that the SSH server is using should be able to tell you what the fingerprint (aka "random hex string") should be for it.
I would rather there be a universal method to convert that hex string into a computed image (maybe LOGO instructions?) It's a lot easier to say "That's the drunken star server" when relating the fingerprint than "It's AE:BB:01:AA:B0 blah blah blah". Any other fingerprint should be fairly unique anyways, generating a (optimally) significantly different image.
-
@Tsaukpaetra Well, I've seen quite a few QR codes in my time, and @ben_lubar's is the only one I can recognize.
-
@Tsaukpaetra Modern version of SSH show the server's key fingerprint as a picture.
-
@anonymous234 said in Arbitrary code execution: Package Manager edition:
It should be relatively easy for the package manager to say "Are you sure you want to install this package with 6 downloads crated yesterday instead of that other one with 2,546,786 downloads created 12 years ago?"
So you want to use something like soundex matching on package names to work out whether to replace one package with another? And that's assuming that the remote service's metadata isn't corrupted at all, since you've got critical scenarios with people wanting legitimately to get things that haven't had masses of prior downloads…
-
@dkf phonograph?
-
-
@dkf said in Arbitrary code execution: Package Manager edition:
@ben_lubar said in Arbitrary code execution: Package Manager edition:
phonograph?
LP or EP?
MF usually, but I'm open to other possib...
Oh, wait, phonograph, not pornography... Never mind.
-
@masonwheeler Surely the same is true about Nuget as well as you can run powershell scripts.
-
@another_sam They would probably work better if they were actual pictures and not ascii art.
Like those automatically generated avatars some blogs used to have.
-
@masonwheeler said in Arbitrary code execution: Package Manager edition:
allow packages with arbitrary names to be uploaded with no manual oversight or code review
and this is the part of this vulnerability that's missing from properly run package repositories like Debian's.
-
@anonymous234 said in Arbitrary code execution: Package Manager edition:
@another_sam They would probably work better if they were actual pictures and not ascii art.
Not on a terminal, which is where I use them, they wouldn't be.
pjh@pjh-thinkpad:~$ ssh what.thedailywtf.com Host key fingerprint is SHA256:lbfSTkH5EFWUJzqnJydZIOyMUB7PlMHH2Ix9AcoUPpw +---[ECDSA 256]---+ | .oo=@+=o++| | .. XB=X o..| | ..+Eoo* ..| | ..o+oo+ | | S . +* | | += o | | .= | | | | | +----[SHA256]-----+ ...pjh@pjh-thinkpad:~$ ssh pjh.homeip.net Host key fingerprint is SHA256:126D4XCESTg5Sn4ChGfbqSNJtZytG0BeaolpZVMyqow +---[ECDSA 256]---+ | o.o.. o. | |..=*+ =. o | |+=O*=o oo . | |*O.+*.. . . | |Eo...o S + . | |o oo = + | | . .o o + | | . . . | | | +----[SHA256]-----+pjh@pjh-thinkpad:~$ ssh -S none hpdesktop.dontexist.com Host key fingerprint is SHA256:PCOOmMdEv82SZlg3uBWf7d441eFpLOnvwOoGq//KqJs +---[RSA 2048]----+ | | | | | . . | | . . o o o . | | . = S o . +.o| | = = X = ..o.=.| | o = O o o o+o | | . o..o. oo+. | | Eooo+=+o.+o | +----[SHA256]-----+
-
@PJH Unless by "terminal" you mean one of those hardware devices from the 80s, your computer screen most likely can display graphics next to the text.
-
@anonymous234 So you're going to require someone to get a GUI working in order to use ssh, even on bridging systems? Way to go increasing the dependency list and complexity for real users.
-
@anonymous234 said in Arbitrary code execution: Package Manager edition:
They would probably work better if they were actual pictures and not ascii art.
But then how would those people who like to pretend it's always 1976 use them? You're talking crazy-talk. Why would anybody use a computer capable of drawing graphics? Pfft.
-
@dkf Naw. Everything's UTF-8 these days, so we'll just start stuffing the randomart with emoji.
-
@flabdablet Something like this?
┏━━━[ECDSA 256]━━━┓ ┃😂 😂 🙌👕 ┃ ┃ 😫 😫 😈💭 ┃ ┃💖👆 👀 ┃ ┃ ┃ ┗━━━━[SHA256]━━━━━┛(with apologies for the issues with alignment if you see them too; the font metrics might be wrong…)
-
@dkf
needs a
-
@Luhmann Yes, but I was getting lazy. :)
-
@dkf said in Arbitrary code execution: Package Manager edition:
require someone to get a GUI working
Oh the horror.
No really, graphics are not complex. Getting a GUI working should not be hard. It's only Linux that insists on treating text as "the normal interface" and GUIs as a second class citizen which is completely wrong and stupid.
But most importantly, this is a client-side thing so you could switch between the text farts or the pictures without changing anything on the server.
-
@anonymous234 said in Arbitrary code execution: Package Manager edition:
Getting a GUI working should not be hard.
It's not colossally complex, but it's a lot more complicated than getting a simple console working. There's a lot more bits and pieces necessarily involved.
-
@anonymous234 said in Arbitrary code execution: Package Manager edition:
No really, graphics are not complex. Getting a GUI working should not be hard. It's only Linux that insists on treating text as "the normal interface" and GUIs as a second class citizen which is completely wrong and stupid.
Here's how to output some ASCII art, with no further compile-time or run-time dependencies:
printf("%s", ascii_art);
Here's how to display a graphical image, after you've found the headers (C is a shitty language) and linked to the library at both compile-time and run-time:
/* Fucked if I know, too long since I ran screaming from Xlib, but you need to create windows and shit */
Congratulations, now your SSH client doesn't even work on a system without X and it's supposed to be a basic system utility. Also it's meant to be secure, so Xlib? Fuck that.
Your graphical image also won't look the same as the ASCII art, making it useless as a quick way of determining if the key is familiar.
Is the ASCII art really so hard to look at that you would break everything else to fix it?
-
@another_sam said in Arbitrary code execution: Package Manager edition:
Is the ASCII art really so hard to look at that you would break everything else to fix it?
I prefer the (hex-encoded) signature bytes.

-
@dkf I don't even see the code. All I see is blonde, brunette, redhead.
-
@another_sam said in Arbitrary code execution: Package Manager edition:
Here's how to display a graphical image,
Filed under: Ok, who decided to photobomb my mockup?!
-
@another_sam Well then fix Linux and C because they're broken.
-
@anonymous234 said in Arbitrary code execution: Package Manager edition:
Well then fix Linux and C because they're broken.
You're doing a @blakeyrat here and assuming that what you want is what everybody wants and what the designers and developers of the software you're using (or not, are you?) want.
In short, you're being entirely unreasonable. You should reconsider.
-
@Tsaukpaetra I hope you remembered to make all the text in that dialogue selectable, or at least have it support that magical "press Ctrl+C in any dialogue to copy all text" shortcut that has never worked for me.
-
@LB_ said in Arbitrary code execution: Package Manager edition:
"press Ctrl+C in any dialogue to copy all text" shortcut that has never worked for me.
The magic Ctrl+C is in a message box - not any dialog.
-
@dcon What's the difference to non-nerds or even nerds who have no familiarity with Windows GUI programming?
-
@anonymous234 said in Arbitrary code execution: Package Manager edition:
@dkf said in Arbitrary code execution: Package Manager edition:
require someone to get a GUI working
Oh the horror.
No really, graphics are not complex. Getting a GUI working should not be hard. It's only Linux that insists on treating text as "the normal interface" and GUIs as a second class citizen which is completely wrong and stupid.
But most importantly, this is a client-side thing so you could switch between the text farts or the pictures without changing anything on the server.
ssh is very easy on the network. I see windows users suffering remote desktop on bad internet daily and that's not fun.
-
@anonymous234 said in Arbitrary code execution: Package Manager edition:
It's only
Linuxworking sysadmins that insistson treating text as "the normal interface" and GUIs asa second class citizen which iscompletely wrong and stupid.Which is why Linux - which has had a comprehensive, usable, scriptable CLI for its entire existence, unlike Windows - is preferred by most sysadmins, given the choice.
-
@fbmac said in Arbitrary code execution: Package Manager edition:
ssh is very easy on the network.
Well, duh, you're talking the difference between transferring text versus images.
-
@fbmac remote desktop worked fine in a modem in the XP era tell the idiots to turn on "best performance" in the options.
-
@lucas1 said in Arbitrary code execution: Package Manager edition:
tell the idiots to turn on "best performance" in the options
It really helps if you get them to work in monochrome. Cuts the bandwidth a lot. Failing that, use 256 color.
-
-
@flabdablet said in Arbitrary code execution: Package Manager edition:
Which is why Linux - which has had a comprehensive, usable, scriptable CLI for its entire existence
Usable?
You do realize you're talking about the culture that originated the term "luser" to hold in utter contempt and derision anyone who can't figure out the arcane gobbledygook that is its command-line interface, right?
-
Full circle, how the fuck is the end user supposed to know what is and isn't right for the picture, when you're talking about people who don't notice a typo?
Images can also be spoofed, so you can create near identical ones if you're not being assigned an image from the package manager itself. Unless the image is true random, it would also be vulnerable to targeted attacks that generates similar images, which is exactly the same attack a typo package uses. You just raise the difficultly one notch.
Or tl;dr
When distributing software in a generic way, you can't protect those who don't give a shit.
-
@Matches said in Arbitrary code execution: Package Manager edition:
Images can also be spoofed, so you can create near identical ones if you're not being assigned an image from the package manager itself. Unless the image is true random, it would also be vulnerable to targeted attacks that generates similar images, which is exactly the same attack a typo package uses. You just raise the difficultly one notch.
The image is just a graphical representation of the public key. It's true that you could get by with a key that is "close enough" to the real thing, but still finding such a key pair would be many orders of magnitude more difficult than picking a similar package name and waiting for the typo. You're still looking at a cryptanalysis/brute force attack.
-
@error it's only an order of magnitude more difficult if both scenarios apply, and in 99%of cases, it won't.
- The user sees the image, and understands what it's for, and knows what the expected image is
- The user actually bothers to validate the image
