:fa_unlock: We might as well stop backing Apple, and Lojban encryption...
-
...what we already have is crap anyway

I just ... I'm so TIRED of this crap! Help me, positive people, help me not to hate everyone today =_=
-
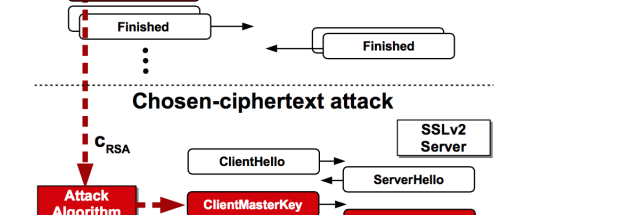
What we have here is some incompetent people still supporting SSLv2, a TLS precursor that was retired almost two decades ago because of weaknesses.
That's like using IE 4 running on Win95 to browse the web today.
-
"Banning strong encryption" is what caused this mess in the first place- yet another vulnerability that depends on oldskool export grade encryption.
If we'd just drop fucking support for that shit entirely already....
Of course, we're liable to need it again here real soon because of Terrists.
-
And by Terrists I mean "pigfuck ignorant politicians"
-
Unrelated, I just added a bunch of Obsolete attributes and NotImplementedExceptions to some scary old encryption algos in my codebase.
All unused since we policy switched to PGP and SSL, but the damn things were still accessible surface area.
-
There are still web servers out there that accept SSLv2 connections? Hell, these days the default is to block both SSLv2 and SSLv3.
-
Representative snippet:
"Matt Green, a cryptography expert at Johns Hopkins University who has read the research paper, told Ars. 'It's amazing to me that we keep finding one or two of these [vulnerabilities] per year for protocols that are this old. This shouldn't keep happening. It kind of makes me feel like we're not doing our jobs.' "
-
 Same with Mint (Intuit).
Same with Mint (Intuit).
This may be a side effect of the corporate proxy that MITMs the fuck out of most SSL connections, but the certificate looks genuine for this one, which suggests it is whitelisted.
-
>It's amazing to me that we keep finding one or two of these [vulnerabilities] per year for protocols that are this old.
Why is this amazing? If a protocol is owned, it's (well, it should be) abandoned, and then who cares how many more times it gets owned, if nobody sensible is still using it?
TLDR: zOMG ownded protocol is owned! hax! amazing!! /dumbass
-
If the idiots who designed this shit would have made it easier to implement, there would be fewer bad implementations of it. It seems obvious but, to crypto developers, it is not.
-
@Vaire said:
>It's amazing to me that we keep finding one or two of these [vulnerabilities] per year for protocols that are this old.
Why is this amazing? If a protocol is owned, it's (well, it should be) abandoned, and then who cares how many more times it gets owned, if nobody sensible is still using it?
TLDR: zOMG ownded protocol is owned! hax! amazing!! /dumbass
To put this into perspective, SSLv3 is older than Internet Explorer. And this exploit is for its predecessor SSLv2.
-
If the idiots who designed this shit would have made it easier to implement, there would be fewer bad implementations of it. It seems obvious but, to crypto developers, it is not.
Only @blakeyrat understands my pain :single tear:
-
I bet we could find terrorists faster just looking on social media and in strip clubs than placing back doors in phones.
And by terrorists I mean both, politicians and extremists.
-
But then you lose security by obscurity...
-
If the idiots who designed this shit would have made it easier to implement, there would be fewer bad implementations of it. It seems obvious but, to crypto developers, it is not.
There are so many things wrong in this post that I don't even want to point them out.
-
@blakeyrat said:
If the idiots who designed this shit would have made it easier to implement, there would be fewer bad implementations of it. It seems obvious but, to crypto developers, it is not.
There are so many things wrong in this post that I don't even want to point them out.If the idiots who designed CPUs would have just made it easier to produce one with a hammer, some wood, and nails, there would be fewer expensive CPUs on the market. It seems obvious, but,, to people who know why computers are complicated, it is not.
-
The problem isn't the difficulty in the algos. The math is the easy part. Get it wrong and you'll generally not be compatible. (Save buffer overflows and other elementary shit)
The recurring nasty parts are the key management, autoconfiguration and all the other ancillary protocol stuff, which very much could have been designed better if cryptogeeks hadn't done it.
The other recurring nasty bit is OpenSSL the library being fucking awful.
-
It must have been designed by open source developers running on Linux hardware
-
Why is this amazing?
Because
it should be) abandoned
but there are a lot of big-name people
still using it
and potentially gettingownded
which is, I think, quite
@tar said:amazing!!
-
I knew it! @abarker is a serious threat to our nation's cyber security.
-
But the quote isn't "it's amazing people keep using these protocols", it's "it's amazing these protocols are still broken". That's not really amazing.
-
Analogy: you have a Yale lock on the door to your apartment. Some nefarious third party uses aan RPG to blast the door off its hinges. Another person then comes up to you and says: 'You have a Yale lock on your door. I can break that! How insecure! Amazing!'
Well, sure, but you're ignoring the fact that the door was already blown off the hinges -- the strength of the lock is a moo point by now.
-
-
-
I don't know, the wording could go either way. The way I interpreted it is "It's amazing that we keep finding vulnerabilities that only work because people keep using these protocols"
-
Cows are like, the discourse of animals, man. Who gives a damn what they think?
-
-
Cows are like, the discourse of animals, man. Who gives a damn what they think?
Almost flagged this for hate speech but then I figured, I didn't care enough whether a cow felt insulted by this or not and that somehow proved your point.
Filed Under: Well played, sir!
-
That's really insulting for cows
But...
Who gives a damn what they think?
So, I think your point is... well... :moon:
-
What we have here is some incompetent people still supporting SSLv2, a TLS precursor that was retired almost two decades ago because of weaknesses.
It's not as if it's that difficult to remove it...
# SSL v2 is seriously flawed: http://en.wikipedia.org/w/index.php?title=Transport_Layer_Security&oldid=630398986#SSL_2.0 # SSL v3 likewise http://en.wikipedia.org/w/index.php?title=Transport_Layer_Security&oldid=630398986#SSL_3.0 (POODLE: CVE-2014-3566) # ./Configure linux-generic32 \ --openssldir=/etc/ssl \ --prefix=/usr shared \ --install_prefix=${INSTALLFS} \ no-ssl2 \ no-ssl3
-
This may be a side effect of the corporate proxy that MITMs the fuck out of most SSL connections, but the certificate looks genuine for this one, which suggests it is whitelisted.
This MITM pisses me off to no end. I have yet to meet a person working in IT security at a corporation that knows how to do anything except use a bunch of purchased tools to fuck with people.
-
This may be a side effect of the corporate proxy that MITMs the fuck out of most SSL connections, but the certificate looks genuine for this one, which suggests it is whitelisted.
That's not an SSLv2 connection, it's TLS1.2 (and the certificate name says SHA2, not SSL2). Chrome disabled everything below TLSv1 ages ago. Microsoft servers don't support those either.
There are still web servers out there that accept SSLv2 connections?
Just like there exists software written by bad developers, there exist deployments maintained by bad sysops. Existing configs on ancient last-updated-in-1999 systems etc.
-
Derp. I saw the "obsolete" and "2" in that context and autocompleted.
The MITM does force SSLv2 on the local leg (or did until recently). It still doesn't support TLS1.2 at all.
-
-
To be fair, if our internal network is compromised, employee comms are the single least valuable target, and SSLv2 is a substantially tougher target than most everything else when you could reach out and grab.... Well, what you can reach out and grab is a Lounge topic.
-

Malvertising over HTTPS is a thing now. You're my least favorite kind of user. I don't like it too, but I don't have another choice. I don't go stealing your passwords.
-
That's definitely TLS 1.2 and not SSLv2 (doesn't it say literally that) and not MITM'd.

-
The MITM does force SSLv2 on the local leg (or did until recently)
No browsers support that, so it likely did not.
It still doesn't support TLS1.3 at all.
Neither do any browsers, since that's still in draft. TLS 1.2 is the newest standard.
-
Fucking mobile fucking keyboard. Meant 1.2
-
From the article, you'd also need to disable all "export grade" ciphers to be safe (Which is default disabled on 1.0.1+) hence they recommands update instead of just disable it on configure.
◦Export cipher suites are disabled by default. [OpenSSL 1.0.2a (current release), OpenSSL 1.0.1m (current release)]
-
Most people should be doing that with the
:!EXPORTdirective in their configs anyways.However, it looks like some versions of OpenSSL can be forced to use disabled ciphers. So the update will still be needed.
-
At some point, they might be able to fix this:
https://www.youtube.com/watch?v=UiJiXNEm-Go
Not in our lifetime...but one day.
-
You're a rare breed. At one place I worked, the security policy prevented the user from changing their password for two weeks after the help desk reset it to password1.
-
I think you have too little confidence in most IT Sec departments...we're not all 'tarded. ;)
-
Aren't more and more sites using DHE/ECDHE key exchanges nowadays? Forward secrecy should protect since this is basically an eavesdropping attack right?
-
Forward secrecy should protect since this is basically an eavesdropping attack right?
If you can't verify the identity of the other party in the communication, there are many trivial attacks possible on SSL and TLS, as you can establish a secure communication with the attacker and they can communicate securely with the legitimate other side. It's just proxying. That's why verifying identity is such an important part of secure communication; without it, you've just got a useless piece of security theatre.
-
If the idiots who designed this shit would have made it easier to implement, there would be fewer bad implementations of it.
Crypto developers tend to be people who make git developers look like they make awesome user interfaces.
-
That's actually what some companies do: The got their AD issue e-cert that can be used as CA and distribute to all machines in the domain as trusted CA, then upload the CA-cert to their specially modified proxy.
When you visit websites using those machines, the browser think they're connecting securely to the target webserver, while in fact the browser is securely connected to the proxy and then the proxy securely connected to the target web server. (You can see the CA of certs are of the company's name) All visits to websites except those on whitelist are side-logged.
-
-
the browser is securely connected to the proxy and then the proxy possibly securely connected to the target web server
FTFY.
 More than 11 million HTTPS websites imperiled by new decryption attack
More than 11 million HTTPS websites imperiled by new decryption attack