OpenSuse 12.3: doing it wrong
-
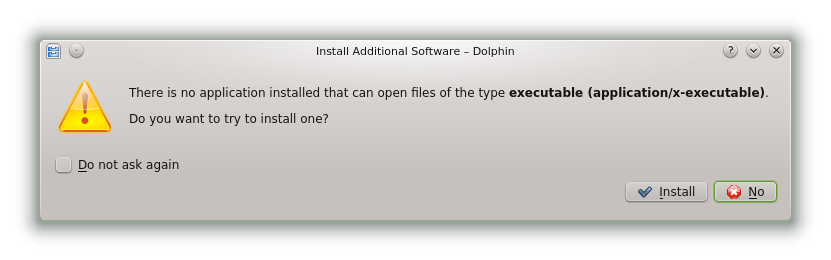
Too funny (and a bit sad) not to post:
-
What have you done?!
I don't have a PC with KDE on my hands atm, so I can't look up if it thinks what it is but ... did you by any chance doubleclick an executable that doesn't have the +x permission?
-
Yes, that's exactly what I did (except it was single click I think).
The very least it should do is detect that special case and show an information message about the missing permission. Unless they think the common user will never have any reason to run raw executable files through the GUI, or that they will never receive one without the permission set.
And then there's the funny Ubuntu systems (maybe not all, but it's happened to me several times) that mount external FAT32 drives and set all files as executable, prompting you every time if you want to run the .txt files or just display them.
-
And then there's the funny Ubuntu systems (maybe not all, but it's happened to me several times) that mount external FAT32 drives and set all files as executable
That’s not just Ubuntu, but every *nix I’ve seen: if the file system doesn’t support permissions, they will all be set so everyone can access anything just like in the OS that the file system originated on. The WTF in the case you describe is that the system checks executability before file association.
-
The WTF in the case you describe is that the system checks executability before file association.
The order is probably this: if actually executable (as determined by theaccess()system call) run it. Otherwise run the MIME-type-determining library on it and use the result to look up what to do.
-
And if you ever saw the MIME-type-determining library, you might just cringe a little.
It is not known as libmagic for nothing.
-
The very least it should do is detect that special case and show an information message about the missing permission. Unless they think the common user will never have any reason to run raw executable files through the GUI, or that they will never receive one without the permission set.
I'm kind of surprised that nobody's made an app that just pops up a dialog box informing the user of that and bound it to the association for application/x-executable.
-
The good ideas thread is this way:



The coding categories are this way:



-
... why would you rip-off the worst bit of OS X 10.2?
-
And if you ever saw the MIME-type-determining library, you might just cringe a little.
I wouldn't. I've already looked and have become… well, inured to the horror. I just don't want to know any more.
-
Reading the manpage on BSD access() just now makes me wonder how what I said differs from what you did.
Also:
CAVEAT Access() is a potential security hole and should never be used.
But I guess it’d be naive to assume people actually heed warnings like this.
-
I wouldn't. I've already looked and have become… well, inured to the horror. I just don't want to know any more.
Yes, the abyss stares back into you.
-
Also:
CAVEAT Access() is a potential security hole and should never be used.
But I guess it’d be naive to assume people actually heed warnings like this.The security hole relates to the fact that there is a gap between when the test is performed and when any action is made predicated on that test. Yet it is still the right test; the only alternative would be to just
execve()and handle the failure, but that's much harder than it appears to be. A non-normativeaccess()check (with theX_OKflag) is the best option.And you still need your code to handle failures. The race condition is real.
-
OK, that makes sense — would have been handy if the man page explained the reason, though, as I doubt it would occur to me if I'd ever have a need to use this.
-
OK, that makes sense — would have been handy if the man page explained the reason, though, as I doubt it would occur to me if I'd ever have a need to use this.
GUIs and stuff like that are the use case, where you need to know if you can execute something without actually doing so. Some people think you can substitute with
stat()(orlstat()orfstat()) but that's not so:access()is allowed to use the ACLs to inform the decision, which thestat()family know nothing about. (Things get even more “fun” with NFS and AFS.)The case where it shouldn't be used is guarding an
open()call. Handling the failure is far better there (though doing so can trip certain kinds of audit logs, which is usually an indication that most people who do software audit have no fucking clue what they're doing, as usual).
-
Said another way: view
access()like you would doing JavaScript validation or checking on a web page. You can put it there as a convenience for the user because of an improved UI -- but it using it as a definitive check for something security-sensitive is a good way to get yourself pwned.
-
Anyone else finds this KDE look totally disgusting? Seriously, KDE could appeal to me, if not for these terrible brown gradients.
-
You can change the theme~
And KDE5 (not the actual name, but I CBA to find the way it's actually called) seems to have a lot fewer gradients in its default style.
-
You can change the theme~And KDE5 (not the actual name, but I CBA to find the way it's actually called) seems to have a lot fewer gradients in its default style.
It was a while back, but I remember trying several things and failing to make it better in any way.
I hope they get with the times, the way it looks now is embarrassing.
-
I hope they get with the times, the way it looks now is embarrassing.
I always switch to the Plastik theme. It's not flashy and is easy to tell what's what.