Is claims based authentication the way to go here?
-
I'm looking into the basic technologies for rewriting a badly made website, and have come across claims based authentication, mainly via a 400 odd page ebook (a guide to claims-based identity and access control) that I don't want to wast too much time digesting if it's not the right approach for the project.
The situation is:
Our customers are businesses, each of which has a few users with their own accounts on the site.
Each business has access to one or more of our products, and each user can have multiple roles (basic user, administrator for that business, handling accounts etc.), so the sections of the site a user can see/access depends on both their business and their roles. There's also a potential requirement to have members of our company authenticated by LDAPS, so when they leave the company and their AD is revoked that covers removing their access to this site as well.
The site will be ASP.Net MVC
The only login systems I have any experience writing are the standard MVC local account ones where you extend the built in account class and give it a
DbContextfor authentication, with a little bit of role management in there.Is claims based a good approach or am I barking up the wrong tree? If it's sensible, are there any guides to get me up and running quickly? If it's not, what's a better approach? Assign roles when a user signs up based on their company's rights?
@magus, I think you've done some WIF stuff IIRC, is this the same sort of thing?
-
@jaloopa So, that's slightly creepily similar to what we have here, but all I have to say on the subject is: Just use Azure ActiveDirectory or something. You don't want to be the one building your access system.
-
@magus said in Is claims based authentication the way to go here?:
Azure ActiveDirectory
We don't have anything on cloud services, it's all data centres and servers we control. Not sure if I'd get approval to add Azure as a dependency...
-
@jaloopa All I know is, handling user identities yourself is dangerous, and about the only people who think it's a good idea anymore are banks, and even they are starting to consider cloud things.
-
@jaloopa A previous employer I worked with started with the default ASP.net claims-based stuff, and we quickly ran into limitations. I'll try to remember some of the scenarios that were troublesome, but bear with me if you think "well you just solve that by x!" it's probably just my bad memory of shit I was dealing with 3 years ago.
We had employees who had to be admins of all clients (present and future), and also employees who were admins to only specific clients, I remember this being a pain to accomplish.
We had:
People -> Clients -> Subclients -> Role(Think of Clients -> Subclients as like "Microsoft" is the client and "Office" is the subclient. You might call them "company and division".)
The problem was we had some huge clients who wanted a:
Clients -> Subclients -> Subsubclients -> Role type arrangement. (This was in healthcare, right? So in our example, even within Microsoft, and even within Microsoft Office, you'd still possibly have multiple healthcare groups. Say "full time" and "contract" groups. Or a union company might have "current employee" and "pension" groups.)
Anyway, we quickly outgrew the default claims-based stuff and kind of ended up writing our own permissions system on top of it.
-
@blakeyrat said in Is claims based authentication the way to go here?:
Anyway, we quickly outgrew the default claims-based stuff and kind of ended up writing our own permissions system on top of it.
Sounds like your system was a lot more complex than this, which means I need to tread the line between YAGNI and future proofing.
Hmm
-
@magus said in Is claims based authentication the way to go here?:
about the only people who think it's a good idea anymore are banks, and even they are starting to consider cloud things.
WTFbank has it's own cloud, with blackjack and hookers
-
@jaloopa said in Is claims based authentication the way to go here?:
Is claims based a good approach or am I barking up the wrong tree? If it's sensible, are there any guides to get me up and running quickly? If it's not, what's a better approach? Assign roles when a user signs up based on their company's rights?
It's good if you have very minimal complexity, don't need to adjust the login info of users currently logged in (i.e. add/remove roles), and don't mind the encrypted box of all the authentication info (which includes claims) for each and every request.
For me in our company, it's fine because we literally only have three roles on the site, but since you have a potential to have federated login, I'd say don't bother with claims at all and let your directory service (whether LDAP, Active Directory, or whatever) take care of permissions.
Here's an old article on how to set up LDAP, I'm sure there are newer packages that make it a bit more straightforward:
-
@tsaukpaetra said in Is claims based authentication the way to go here?:
but since you have a potential to have federated login, I'd say don't bother with claims at all and let your directory service (whether LDAP, Active Directory, or whatever) take care of permissions.
That would mean setting up trusts between the AD of @Jaloopa's employer and their customers. That's not something which you should want. Claims based authentication is definitely the way to go here, this allows customers to stay in control over their users (and roles) while you don't have to worry about authentication either.
You don't need Azure Active Directory, you can build anything you want without having to rely on their
clowncloud service offerings. AAD is nice because it offers a great deal of control in a relatively simple interface, it does a lot of the heavy lifting for you.
-
TIL something about claims based authentication.
That still leaves the question of authorization mechanism, but something like this could be useful for my product.

-
If you're doing claims-based authentication, the claims are really only accessible at runtime, correct? If you want a list of "all users who can access X", you'd have to go query AD to find the group members?
-
It depends. With Azure AD, you can use the Graph API to get information about users and groups present in the directory. If users are coming from other systems it can be difficult to impossible, as there is no standardised "give me all users" mechanism. Just like there is no "give me all Facebook/Twitter/Snapchat/Tinder users" API.
There are basically two alternatives:
- You invite users yourself, e.g. by inputting an e-mail address somewhere which then sends a "Hey, check out my app" message.
- The IdP can push users into the system (provisioning) so that access can be granted shortly after the identity has been created in the store.
-
@unperverted-vixen said in Is claims based authentication the way to go here?:
If you're doing claims-based authentication, the claims are really only accessible at runtime, correct? If you want a list of "all users who can access X", you'd have to go query AD to find the group members?
With claims, if you have access to the underlying datastore I don't see why not.
For instance, in my app I'm storing Steam IDs as a claim so they can login using Steam (account gets auto-created if it doesn't exist). If we promote them to Mod we add the Mod role to them.So, to find all users who have Steam authenticated and are mods, I'd do something like:
Select Username from AspNetUsers an join AspNetClams ac on an.ID = ac.AspNetID and ac.ClaimName = 'Steam' jon AspNetRoles ar on an.ID = ar.AspNetID and ar.RoleID = '{GUID Here}'If you shove the role federation on another system, then like @AlexMedia said there's likely a similar method to get user information from that system.
@alexmedia said in Is claims based authentication the way to go here?:
That would mean setting up trusts between the AD of @Jaloopa's employer and their customers.
I didn't read that like that in the OP, it sounded to me that they wanted internal employees to have access the the app, not that the customer's directories would be federated.
-
@tsaukpaetra You've gotta jon those AspNetClams.
-
@ben_lubar said in Is claims based authentication the way to go here?:
@tsaukpaetra You've gotta jon those AspNetClams.
No gotta get a new laptop battery so t stops killing my I and W keys.
-
@tsaukpaetra said in Is claims based authentication the way to go here?:
AspNetClams
I always thought clams were caught by digging them up, not with nets. And certainly not with a net made of venomous snakes!

-
@masonwheeler said in Is claims based authentication the way to go here?:
I always thought clams were caught by digging them up, not with nets. And certainly not with a net made of venomous snakes!
HIS I KEY DOESN'T WORK BECAUSE HIS LAPTOP HAS A BAD BATTERY! AN EXPLANATION THAT MAKES PERFECT SENSE!
Leave the man alone. I mean, sometimes my Q key doesn't work because there are an even number of dogs in the Bangkok park system.
-
@blakeyrat said in Is claims based authentication the way to go here?:
@masonwheeler said in Is claims based authentication the way to go here?:
I always thought clams were caught by digging them up, not with nets. And certainly not with a net made of venomous snakes!
HIS I KEY DOESN'T WORK BECAUSE HIS LAPTOP HAS A BAD BATTERY! AN EXPLANATION THAT MAKES PERFECT SENSE!
Leave the man alone. I mean, sometimes my Q key doesn't work because there are an even number of dogs in the Bangkok park system.
Lemme see your bulging keyboard that still works perfectly. I'm rather surprised the thing still works, actually. The screen doesn't even close to an inch at the moment.
-
@tsaukpaetra Want to borrow Daisy? She has a working I and U key. No E or up/down arrows, though.
-
@ben_lubar said in Is claims based authentication the way to go here?:
@tsaukpaetra Want to borrow Daisy? She has a working I and U key. No E or up/down arrows, though.
I've never done a duck before. Sure!
-
@tsaukpaetra said in Is claims based authentication the way to go here?:
@ben_lubar said in Is claims based authentication the way to go here?:
@tsaukpaetra Want to borrow Daisy? She has a working I and U key. No E or up/down arrows, though.
I've never done a duck before. Sure!
https://what.thedailywtf.com/topic/23139/goodbye-daisy-hello-edgar
-
@tsaukpaetra said in Is claims based authentication the way to go here?:
AspNetClams
And how many AspNetClams will that cost me?!
 d of course
d of course
-
@darkmatter said in Is claims based authentication the way to go here?:
And how many AspNetClams will that cost me?!
Ask Jon. He knows.
-
@tsaukpaetra said in Is claims based authentication the way to go here?:
Lemme see your bulging keyboard that still works perfectly.
Wait, the battery's bulging? Like physically? Is it lithium-ion? I'm pretty sure you're about to die.
-
@blakeyrat said in Is claims based authentication the way to go here?:
@tsaukpaetra said in Is claims based authentication the way to go here?:
Lemme see your bulging keyboard that still works perfectly.
Wait, the battery's bulging? Like physically? Is it lithium-ion? I'm pretty sure you're about to die.
Hmmm. You know, I haven't tested my flame resistance in a while.
Point, would rather it be done in a more controlled manner though.Yes, the pack has bulged, the capacity has thus reduced from about five hours to about two. I just haven't ordered a replacement yet, been in tight budget mode from the layoff situation.
-
If the battery is bulging I wouldn't risk continued use of said laptop and battery. Instead, I'd store everything in a safe location and contact the manufacturer.
-
@alexmedia said in Is claims based authentication the way to go here?:
store everything in a safe location
Where would you consider "safe"?
and contact the manufacturer.
.... Why? This thing is more than three years old. What would you expect them to do?
-
I would go for a shed.
And if it's that old it's most likely to be out of warranty. In that case I'd take the whole thing to a nearby waste disposal site, ask them to take out the battery (as it might be damaged) and keep the rest.
I would definitely not keep using it. It's a fire hazard.
-
@alexmedia said in Is claims based authentication the way to go here?:
It's a fire hazard.
It's been a fire hazard for at least three months then.
@alexmedia said in Is claims based authentication the way to go here?:
a nearby waste disposal site
Searching "waste disposal site"...
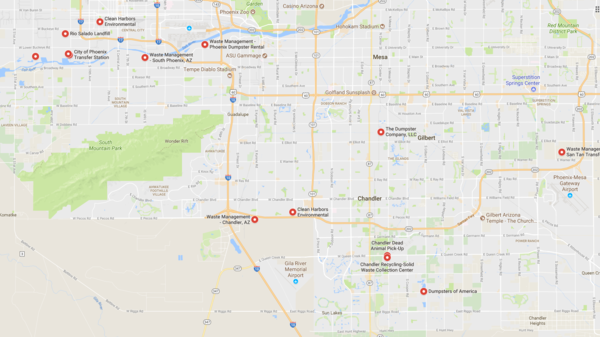
Nearby does not match any found object descriptors.
@alexmedia said in Is claims based authentication the way to go here?:
ask them to take out the battery (as it might be damaged)
I can (and have) removed it previously in about 20 minutes after exploratory evaluation. Why would I waste time with waste disposal employees, who would not likely return my device in the same functioning state it is currently.
@alexmedia said in Is claims based authentication the way to go here?:
not keep using it
The most likely explanation why it's expanded is due to overcharging caused by not using it, actually.
-
@tsaukpaetra ... it seriously is a big safety issue.
-
@blakeyrat said in Is claims based authentication the way to go here?:
@tsaukpaetra ... it seriously is a big safety issue.
I apprecate that you care so much.

-
Well, if @Tsaukpaetra suddenly stops posting one day, we'll all know what happened...
-
I am confused (not surprising, it has been a long day)... Are we talking about Authentication or Authorization? Claims Based Authentication is typically associated with Federated Identities and SSO... Authorization is typically associated with systems like RBS [Role Based Security]....
-
@masonwheeler said in Is claims based authentication the way to go here?:
Well, if @Tsaukpaetra suddenly stops posting one day, we'll all know what happened...
What?!?! What happened??? I'm dying to know!
-
@thecpuwizard said in Is claims based authentication the way to go here?:
Are we talking about Authentication or Authorization? Claims Based Authentication is typically associated with Federated Identities and SSO... Authorization is typically associated with systems like RBS [Role Based Security]
This pay be part of my confusion. I think I've kind of conflated the two in my head.
From your summary there, I think authorisation is what I was thinking of. Letting users access different parts of the system depending on their roles and companies.
I think the LDAP thing has been shot down now. Opening up a website that's on the wide open internet to our AD is not going to get past any sort of security audit. There's now talk of checking with a different back end system to see whether they have an account with that system, on login and account creation. That leaves just the access to parts of the application, not general application access
-
@tsaukpaetra said in Is claims based authentication the way to go here?:
@masonwheeler said in Is claims based authentication the way to go here?:
Well, if @Tsaukpaetra suddenly stops posting one day, we'll all know what happened...
What?!?! What happened??? I'm dying to know!
Background processing completed. I assume you were talking about the potential fire hazard from incendiary battery events. Rest assured this has not happened.
Also, shipment arrived!
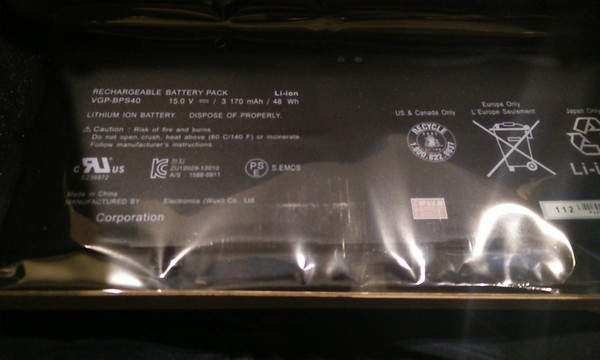
Installation in progress...
