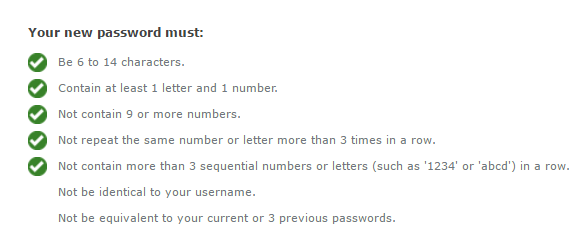
Guess the WTF from the password requirements
-
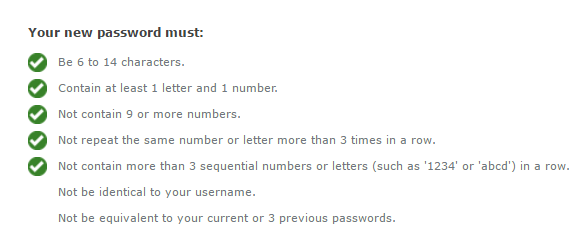
What kind of WTF systems require the password to not have 9 or more numbers?
-
Maybe they're running into problems with floating point rounding.

-
@Yamikuronue This looks like its on some online service.
These constraints are supposedly meant to protect from a brute-force attack on the password.
But this is an online service - its their job to rate-limit the login form to prevent brute force attack.So by this they mean that they can not detect/prevent someone from trying the whole dictionary on their site? Oh someone tried to log in 100 times today using passwords from this known password dictionary - we surely need to allow him to keep doing this.
-
@Adynathos said in Guess the WTF from the password requirements:
This looks like its on some online service.
It's a bank. A bank I'm in the process of removing my money from.
-
@Yamikuronue said in Guess the WTF from the password requirements:
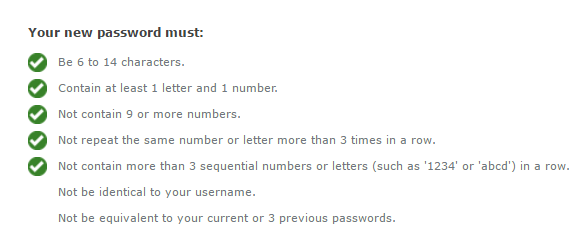
What kind of WTF systems require the password to not have 9 or more numbers?
These password requirement rules are always stupid and
 . Something simple to prevent 123456 is the only one that might make sense.
. Something simple to prevent 123456 is the only one that might make sense.
-
@Yamikuronue said in Guess the WTF from the password requirements:
A bank I'm in the process of removing my money from.
You can remove money from other users as well. Surely if you read all the password constraints carefully, it turns out there are just 3 different passwords possible that satisfy all of them.
-
So they store four passwords for each user?
-
@Yamikuronue said in Guess the WTF from the password requirements:
It's a bank. A bank I'm in the process of removing my money from.
A bank? Good luck with remembering those "security" questions you set years ago
-
@Sumireko I got in with no problem. They did ask about my previous addresses though.
-
@Adynathos so,
hunter1,*******andhunter3?
-
@Yamikuronue said in Guess the WTF from the password requirements:
What kind of WTF systems require the password to not have 9 or more numbers?
You can apparently improve security by removing all but 5 of those numbers (and the one letter).
-
I came up with an answer, and the more I thought of it the more I realized there were deeper, darker layers in play. Imma just going to post before I go complete insane.
It all comes down to math.
On the surface: Max 14 characters. If you had 9 numbers, you'd only have 5 letters. I bet a manager somewhere said 5 letters isn't a strong enough password, because six is a number that I see all the time as the minimum. Of course forgetting that those letters and numbers combine to form complexity.
But then some of the other requirements seemed too coincidental. Specially the "can't have more than 3 sequential numbers in a row".
Path of Insanity 1: Stacked against sanity
How do you determine if something is sequential? Well, is it one greater than the character before it? So not only do you have to keep track of the first number in a series, but also have to backtrack each time you encounter a new number.
Now the smart way of doing that is note the ASCII code of current character. Start a counter. Move to next character. If ASCII Code -1 == last ASCII code, add one to a counter ELSE reset counter. If counter is
>max, error.That's the SMART way. The CLEVER way would be to start a stack of some sorts. Each time a number pops up, cast it to an int, and start a stack for it. Start stacking numbers on that stack as they sequentially appear. And to be even more clever, determine sentimentality with a MOD, so that 9012 is a sequential series.
Uh oh, QA just tried 01234567890. The 0 stack backtraced back to itself and started an infinite recursion, overloaded the stack and crashed the entire web server! Should we re-think this? No, instead say no one can put in more than 9 numbers in a row. The user is Doing It Wrong!
Path of Insanity 2: R. Re. Reg. Rege. Regex. e. eg. egr. ege. egex. egexR. g. ge. gex. gexR. gexRe
So even more CLEVER than a stack is a regex, of course. They probably used regex to validate all the other requirements. [0-9]{0,8} for "no more than nine numbers". (note: yes, I know this is wrong). So of course, let's make sure we use one tool for the whole job.
Okay, how do you determine sentimentality with a regex? I'm sure there's a way, but we know the CLEVER way.
[0][1][2][3]See, that means someone entered more than 3 sequential numbers! So just go ahead and type in the rest of the sequences.
([0][1][2][3]|[1][2][3][4]|[2][3][4][5])And so forth. But shit, remember the clever bit about wraparound. We also have to check 9012. I think you can see the regex getting kind of big at this point.
But now someone comes along and says "Wait, we shouldn't be blacklisting sequences AND whitelisting? What if there's a bad sequence we forgot about? What if there's a good one?" Because who knows when someone might invent a new digit?
Okay, time to whitelist and blacklist. The whitelist is "easy" enough. 1. 12. 123. 2. 23. 234. Etc.
The blacklist is also "easy" enough. 1234. 12345. 123456. 1234567. 12345678. 123456789. 123456789.
Using capture groups, of course.
But QA, those fucking assholes, ruin everything again. "What about 123456789012345678901234567890".
The performance of this regex is already bullshitty shit shit because of the 70+ blacklist and 30+ whitelist regex clauses. We can't start adding additional clauses to check for 1234567890 and 12345678901 and 123456789012. There is literally no end!
So instead, just straight up say you can't enter 9 or more numbers anywhere in the password. There, the CLEVER solution survives, and the user is DOING IT WRONG.
Path to insanity 3: special sanity
wait there's no requirements or restrictions for special characters do they not know how those work or are sequential oh god what happens when someone realizes @bcd is like sequential abcd and then then we need l33t regex checkers and omg ahhhhhhhhhhhhhhhhhhhhhhhhhhhhhhhhhhhhhhhh
-
it's 14 characters because the SSO endpoint doesn't actually reserve memory correctly so going over 14 ends up ruining the stack and dave said not to touch that code because we don't have the budget for it
-
@coldandtired said in Guess the WTF from the password requirements:
So they store four passwords for each user?
It's a common requirement. We just store the last however many bcrypt hashes the system is configured to remember and check against them when a user changes passwords.
-
@boomzilla said in Guess the WTF from the password requirements:
@coldandtired said in Guess the WTF from the password requirements:
So they store four passwords for each user?
It's a common requirement. We just store the last however many bcrypt hashes the system is configured to remember and check against them when a user changes passwords.
You do.
Wanna bet that they store the passwords in a reversible manner, so that they can ensure your new password isn't "too similar" to your old one?
(rather than transforming your new password, hashing it, and seeing if it matches your old hash...)
-
@Lorne-Kates said in Guess the WTF from the password requirements:
Wanna bet that they store the passwords in a reversible manner, so that they can ensure your new password isn't "too similar" to your old one?
No
-
-
@PJH said in Guess the WTF from the password requirements:
@boomzilla said in Guess the WTF from the password requirements:
No
Why? You'd surely win!
Even so, I'm sure we all know what @Lorne-Kates' response would be...
-
@Lorne-Kates said in Guess the WTF from the password requirements:
@boomzilla said in Guess the WTF from the password requirements:
@coldandtired said in Guess the WTF from the password requirements:
So they store four passwords for each user?
It's a common requirement. We just store the last however many bcrypt hashes the system is configured to remember and check against them when a user changes passwords.
You do.
Wanna bet that they store the passwords in a reversible manner, so that they can ensure your new password isn't "too similar" to your old one?
(rather than transforming your new password, hashing it, and seeing if it matches your old hash...)
I want to bet they store it in a reversible manner to check that you haven't reused passwords, but that similarity tests are beyond them, does that count?
-
@Yamikuronue said in Guess the WTF from the password requirements:
@Adynathos said in Guess the WTF from the password requirements:
This looks like its on some online service.
It's a bank. A bank I'm in the process of removing my money from.
Ohhh! So close!
-
@boomzilla said in Guess the WTF from the password requirements:
Even so, I'm sure we all know what @Lorne-Kates' response would be...
Fuck you, give me money?
-
@Yamikuronue TRWTF is the 14 character limit.
-
@Yamikuronue said in Guess the WTF from the password requirements:
What kind of WTF systems require the password to not have 9 or more numbers?
Ones that don't want users to use their phone number as their password.
-
@anotherusername Is... that a common problem?
-
@Yamikuronue now I'm wondering if they're not actually trying to prevent people using their SSN...
-
@anotherusername Or their bank account number?
-
@Yamikuronue said in Guess the WTF from the password requirements:
@anotherusername Is... that a common problem?
Iunno about southern Canada, but here in western Lithuania it's very common for people to use year of birth as PIN and city of origin as password.
-
@anotherusername said in Guess the WTF from the password requirements:
@Yamikuronue now I'm wondering if they're not actually trying to prevent people using their SSN...
I was just about to say that. I bet that was the standard in the past and they wanted to enforce it not being allowed.
-
This post is deleted!
-
@Yamikuronue said in Guess the WTF from the password requirements:
@anotherusername said in Guess the WTF from the password requirements:
their SSN...
Seven digits tho?
[-0-9]
Negative numbers are numbers too.
-
@dangeRuss yeah I somehow fucked up how long SSNs were ,ignore me
-
@Yamikuronue said in Guess the WTF from the password requirements:
@dangeRuss yeah I somehow fucked up how long SSNs were ,ignore me
You managed to convince me for a minute
-
@Gąska said in Guess the WTF from the password requirements:
Iunno about southern Canada, but here in western Lithuania it's very common for people to use year of birth as PIN and city of origin as password.
Just these days I talked a school director out of using the school's name + "2016" for the web site password, "because it's easy to remember".
TRWTF is systems using inane rules instead of cracklib. Just let the user use whatever and if it's too easy, error out with "It took us 0.0038 seconds to guess this password. How long do you think it will take a hacker?"
-
@dangeRuss said in Guess the WTF from the password requirements:
Negative numbers are numbers too.
If we're going by that logic, then I should be able to use 1234567890.
1,234,567,890
One billion, two hundred thirty-four million, five hundred sixty-seven thousand, eight hundred and ninety is just one number.
-
This post is deleted!
-
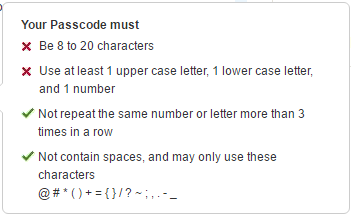
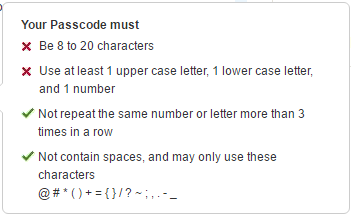
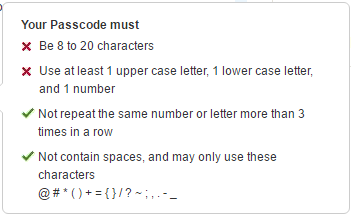
@Tsaukpaetra How is it possible to include at least 1 number when there is not a single number on the list of allowed characters?
-
@Tsaukpaetra said in Guess the WTF from the password requirements:
@Yamikuronue said in Guess the WTF from the password requirements:
@Adynathos said in Guess the WTF from the password requirements:
This looks like its on some online service.
It's a bank. A bank I'm in the process of removing my money from.
Ohhh! So close!
There are no upper or lower case letters or numbers in the list of allowed characters.
-
@martijntje said in Guess the WTF from the password requirements:
@Tsaukpaetra How is it possible to include at least 1 number when there is not a single number on the list of allowed characters?
Leaving out the letters, are you?

Filed under;; #letterlivesmatter
-
@Yamikuronue I would imagine so, yes.
-
@ben_lubar they meant, "may only use these symbols (in addition to the alphanumeric characters)".
-
@JazzyJosh said in Guess the WTF from the password requirements:
@Yamikuronue TRWTF is the 14 character limit.
Often a sign that they don't hash the password.
-
@boomzilla said in Guess the WTF from the password requirements:
@Lorne-Kates said in Guess the WTF from the password requirements:
Wanna bet that they store the passwords in a reversible manner, so that they can ensure your new password isn't "too similar" to your old one?
No
One third-party thing my company uses demands new passwords be "not too similar" with the old one (which you have to type on the same form that allows you to specify the new one) and not equal to the last 5 or so ones, which seems to imply that at least they do only store hashes.
Still a pain in the ass though, so clever users work around such requirement with MyPassword1, CorrectHorseBatteryStaple2, MyPassword3, CorrectHorseBatteryStaple4, etc.
-
@Yamikuronue said in Guess the WTF from the password requirements:
What kind of WTF systems require the password to not have 9 or more numbers?
I guess it's because they allow only up 14-character long passwords. Which is one of the biggest WTF's out there.
-
@Medinoc said in Guess the WTF from the password requirements:
Often a sign that they don't hash the password.
char password[15]; sscanf("%s", password);
-
@Tsaukpaetra said in Guess the WTF from the password requirements:
@Yamikuronue said in Guess the WTF from the password requirements:
@Adynathos said in Guess the WTF from the password requirements:
This looks like its on some online service.
It's a bank. A bank I'm in the process of removing my money from.
Ohhh! So close!
What's the deal with prohibiting space characters? I get the
 reason for the max length, and for some prohibited characters, but I've never understood wtf that restriction ever existed.
reason for the max length, and for some prohibited characters, but I've never understood wtf that restriction ever existed.
-
@Dreikin said in Guess the WTF from the password requirements:
What's the deal with prohibiting space characters? I get the
 reason for the max length, and for some prohibited characters, but I've never understood wtf that restriction ever existed.
reason for the max length, and for some prohibited characters, but I've never understood wtf that restriction ever existed.md5sum <<<$passwordg,d&r
-
@LaoC said in Guess the WTF from the password requirements:
@Dreikin said in Guess the WTF from the password requirements:
What's the deal with prohibiting space characters? I get the
 reason for the max length, and for some prohibited characters, but I've never understood wtf that restriction ever existed.
reason for the max length, and for some prohibited characters, but I've never understood wtf that restriction ever existed.md5sum <<<$passwordg,d&r
Uh, which language uses
<<<? Is it PHP? It's PHP, isn't it? Belgium dammit, PHP.
-
@Dreikin bash herestring.
-
@PleegWat PHP also has herestring though they're not called that...
-
@PleegWat said in Guess the WTF from the password requirements:
@Dreikin bash herestring.
Not much better, really.
Filed under::
() { :; };